Introduction :
Ethical hacking entails a legitimate attempt to access a computer system, application, or data without authorization.
Ethical hacking tools play a significant role in testing weaknesses in the computer network and applications.
It involves copying the tactics and behaviors of malicious attackers to carry out ethical hacking.
This procedure aids in locating security flaws that can be fixed before a malicious attacker can take advantage of them.
To test the system’s defenses, the company that owns the system or network permits ethical hackers to carry out such activities.
This means that, in contrast to malicious hacking, the process is organized, approved, and, more importantly, ethical.
Investigating the system or network for vulnerabilities that malicious hackers can take advantage of or obliterate is the goal of ethical hackers.
By doing this, they can strengthen the security footprint and make it more resistant to attacks or able to deflect them.
What is the Most Common Form Used by Hackers?
The method of hacking that is used the most is phishing.
Every day, phishing messages saturate every one of our inboxes and text messaging applications.
These messages pretend to be from a company (such as Amazon, Netflix, etc.) or a friend you trust.
They usually tell a story to get you to open an attachment or click on a link.
An attack that tries to steal your money or your identity by tricking you into disclosing personal information, like credit card numbers, bank account information, or passwords, on websites that look legitimate but are fraudulent.
What Sites Get Hacked The Most?
30,000 new websites are compromised every day on average.
With an increase from 39.5% at the end of 2020, WordPress now powers 43.2% of websites online.
WordPress is most at risk from the extensive selection of third-party plugins that users use.
Many WordPress website owners and developers have experienced attacks because of plugin vulnerabilities.
Because of their enormous user base, WordPress websites are a prime target for hackers.
15 Best Ethical Hacking Tools
- Wireshark
- NMAP
- Burp Suite
- Metasploit
- Nikto
- Intruder
- Aircrack-Ng
- Nessus
- Acunetix
- SQLMap
- Angry IP Scanner
- QualysGuard
- Invicti
- OpenVAS
- ettercap
Table of Contents
What is the Most Common Form Used by Hackers?
What Sites Get Hacked The Most?
15 Best Ethical Hacking Tools
1.Wireshark
2.NMAP
3.Burp Suite
4.Metasploit
5.Nikto
6.Intruder
7.Aircrack-Ng
8.Nessus
9.Acunetix
10. SQLMap
11.Angry IP Scanner
12.QualysGuard
13.Invicti
14.OpenVAS
15.ettercap
15 Best Ethical Hacking Tools Features
Frequently Asked Questions
Also Read
15 Best Ethical Hacking Tools Features
| Best ethical hacking Tools | Key Attributes |
| 1. Wireshark | 1. Display Filters 2. Packet Reconstruction 3. Statistics and Graphs 4. Multiple protocol decryption 5.Getting captured info out in different formats |
| 2. NMAP | 1. Host Discovery 2. Port Scanning 3. Service and Version Detection 4. Operating System Detection 5.Scan types and settings that can be changed |
| 3. Burp Suite | 1. Intercepting Proxy 2. Web Application Scanning 3. Targeted Manual Testing 4. Helper for advanced tests and reporting 5.Being able to add on by using plugins |
| 4. Metasploit | 1. Exploit Development and Testing 2. Exploit Modules 3. Payloads 4. Post-exploitation Modules 5.Modules made by the community |
| 5. Nikto | 1. Comprehensive Scanning 2. Vulnerability Detection 3. SSL/TLS Testing 4. Configuration Checks 5.Support for various plugins/configs |
| 6. Intruder | 1. Packet Capture and Analysis 2. WEP/WPA/WPA2 Key Recovery 3. de-authentication and Disassociation Attacks 4. Rogue Access Point Detection 5.Compatible with other security frameworks |
| 7. Aircrack-Ng | 1. Packet Capture and Analysis 2. WEP/WPA/WPA2 Key Recovery 3. de-authentication and Disassociation Attacks 4. Rogue Access Point Detection 5.With acquired data, break passwords offline |
| 8. Nessus | 1. Vulnerability Scanning 2. Plugin Architecture 3. Compliance Auditing 4. Credential-based Scanning 5.On-demand and scheduled scanning |
| 9. Acunetix | 1. Comprehensive Vulnerability Scanning 2. Deep Crawling and Scanning 3. OWASP Top 10 and PCI DSS Compliance Checks 4. Advanced Manual Testing Tools 5.AcuSensor Technology detects vulnerabilities |
| 10. SQLMap | 1. Automated SQL Injection Detection 2. Multiple Database Support 3. Fingerprinting and Enumeration 4. Full Database Dumping 5.A list of databases, tables, columns, and data |
| 11. Angry IP Scanner | 1. Fast IP Address Scanning 2. Host Discovery 3. Custom IP ranges and scanning settings 4 Host Information Gathering 5.Lightweight, portable app |
| 12. QualysGuard | 1. Vulnerability Assessment 2. Continuous Monitoring 3. Asset Discovery and Inventory 4. Policy Compliance 5.Threat defense and responding to incidents |
| 13. Invicti | 1. Web Application Vulnerability Scanning 2. Deep Scanning Capabilities 3. Interactive Application Security Testing (IAST) 4. Customizable Scan Policies 5.Instructions for fixing problems and ways to report them |
| 14. OpenVAS | 1. Vulnerability Scanning 2. Network Discovery 3. Web Application Scanning 4. Credential-based Scanning 5.Open-source software that is changed often. |
| 15. Ettercap | 1. Display Filters 2. Packet Reconstruction 3. Statistics and Graphs 4. VoIP Analysis 5.Attack possibilities that can be changed |
1 – Wireshark

Gerald Combs started developing Wireshark in late 1997 under the name Ethereal because he needed an ethical hacking tool to find problems with networks.
The project changed its name to Wireshark in May 2006 because of trademark problems.
Among network protocol analyzers, Wireshark stands head and shoulders above the competition.
Software developers utilize it for analysis, communication protocol development, and network troubleshooting.
We may tailor it to our specific needs by watching the packets and filtering them individually.
Another group that made use of Wireshark to look for security holes were ethical hackers.
Wireshark is a favorite among network enthusiasts, administrators, engineers, and even malicious hackers due to its ability to monitor a wide variety of network standards, including ethernet, WLAN, Bluetooth, and more.
By letting you filter and drill down into your network traffic, this tool aids in network analysis and, eventually, network security.
Features
- It is a normal packet analyzer with three panes.
- The software works on many different operating systems, including Linux, Windows, OS X, FreeBSD, NetBSD, and more.
- Real-time traffic recording and analysis
- A close look at hundreds of rules.
| What is Good ? | What Could Be Better? |
|---|---|
| Identifies the protocol generating the packets. | Can’t send packets |
| Enables packets to be sorted, grouped, and filtered. | Can’t alter packets or generate them. |
| Help networking analysts identify any security issues and resolve latency problems. | It takes time to find what you are actually looking for due to the abundance of network information. |
| Exporting packets for analysis in other utilities. | Cannot alter or manipulate data or objects on the network. |
Price
You can get a free trial and personalized demo from here.
2 – Nmap

Nmap, created by Gordon Lyon, is a free and independent program for auditing and scanning networks.
Network discovery is made easy with Nmap.
A network administrator can utilize Network Mapper in their networked system to identify and analyze services operating on a system linked to the Internet in order to identify and fix possible security vulnerabilities.
Using it, network managers can identify the devices connected to a system, as well as the services and versions operating on it, as well as the port number.
It was designed to scan vast networks quickly, but it works effectively against a single host.
Originating on Linux, Nmap has now been ported to several operating systems including Windows, macOS, and BSD.
Its popularity on Linux is second to that on Windows.
Features
- Nmap saves scan data in plain text, XML, grepable, and more.
- Interactively writing commands and arguments on the command line makes real-time adjustments and experiments easier.
- Nmap works fast and well.
- It’s portable and supports numerous operating systems.
- Nmap can be connected to other security systems and tools to improve their integration or leverage its scanning features in a larger security procedure.
| What is Good? | What Could Be Better? |
|---|---|
| Network Mapper will search for subdomains and the Domain Name System (DNS). | It takes some time to get comfortable with the options and the solutions. |
| Large networks with literally hundreds of thousands of machines have been scanned using Nmap. | It’s possible that scanning is hostile. |
| Network Inventory, Network Mapping, maintenance, and asset management. | Some systems have been known to crash after SYN scans. |
| Identifying new servers and performing a network security audit. |
Price
You can get a free trial and personalized demo from here.
3 – BurpSuite
.webp)
When it comes to doing a penetration test on a web site, Burp Suite is a fully-featured scanning tool that can handle about anything you could possibly require.
The creator, Dafydd Stuttard, goes by the alias “Port Swigger” when he runs the company that makes it.
When it comes to web app security and bug bounty hunting, it is the tool that specialists utilize the most.
When compared to free alternatives like OWASP Zap, it is much easier to use and hence more suitable.
A Scanner, Spider, Proxy, Intruder, Repeater, Decoder, and Extender are just a few of the tools included in Burp Suite.
You can install BApps to expand the functionality of Burp Suite, which aims to be an all-inclusive set of tools.
Features
- Watch, read, and change browser-to-app web data.
- Web apps can have SQL injection, XSS, and other bugs identified automatically.
- Finds and maps web app functionalities.
- Customizable web service exploits exploit security weaknesses.
- Allows manual HTTP request changes and resending for testing.
| What is Good? | What Could Be Better? |
|---|---|
| Best and basic pentesting tool for information security. | The software’s presentation should be more representative and improvised. |
| Automated bulk scanning and simulated scenarios. | Plugins must be manually updated without network connectivity. |
| BurpSuite is a robust tool for online application vulnerability scanning, penetration testing, etc. | |
| Users can design and use plugins and extensions to customize and add features. |
Price
You can get a free trial and personalized demo from here.
4 – Metasploit

Computer security efforts like the Metasploit Project help with things like penetration testing, creating intrusion detection system (IDS) signatures, and sharing information on security gaps.
Malicious and ethical hackers alike can use the Metasploit framework to their advantage while looking for server and network security flaws.
Since the open-source community and Rapid 7 have joined forces, Metasploit has expanded the capabilities of security teams beyond vulnerability verification, awareness-raising, and assessment management.
About 500 payloads and 1,677 exploits are now organized in Metasploit, which covers 25 platforms. These platforms include Android, PHP, Python, Java, and more. Metasploit contains several different components, including exploits, payloads, encoders, listeners, and more.
Features
- Very many exploits, payloads, and supplementary tools are known.
- Makes firearms for various targets and scenarios.
- Many flaws can be utilized to uncover and exploit system weaknesses.
- Get information, increase rights, and maintain access.
| What is Good? | What Could Be Better? |
|---|---|
| As it is mostly CLI driven, there is very limited GUI-based utility. | Metasploit can cause the system to crash if it is not used properly. |
| Automation of manual tests and exploits enables what used to take days off work to be completed in a matter of hours. | Option for payload management. |
| Separate workspace for different projects. | As it is mostly CLI driven, there is very limited GUI based utility. |
| The database of exploits is updated. | Integrating the results with reporting tools or exporting the outcomes. |
Price
You can get a free trial and personalized demo from here.
5 – Nikto

Nikto is an open-source command line vulnerability scanner that can scan web servers for malicious files/CGIs, incorrectly configured services, scripts that are vulnerable, and other vulnerabilities.
The design of this gadget does not prioritize becoming unnoticeable.
You can see the findings of a web server scan in log files or on an IPS/IDS system right away.
Additionally, we have searched the log files for certain factors that remain a mystery.
The great majority of checks are not secure, however there are a few exceptions.
It scans the system for pre-installed applications and web servers.
Additionally, we verify the server’s configuration elements, including the HTTP server settings.
Nikto scans should be detectable by intrusion detection systems that are set up to monitor web server logs, whether they are host-based or network-based.
Features
- Over 6700 dangerous files and CGIs can be found by Nikto.
- Frequently updated scan items and apps can self-update.
- Nikto can check 1200 sites for outdated versions.
- Check multiple server ports or hosts and Nmap files.
| What is Good? | What Could Be Better? |
|---|---|
| Full HTTP proxy support. | No GUI interface. |
| Results saved in multiple formats (XML, HTML, NBE, OR CSV) | Development and support should be available. |
| External checks for web applications are there | Without a paid vulnerability list, this won’t work. |
| Nikto checks for common “parking” sites. |
Price
You can get a free trial and personalized demo from here.
6 – Intruder
One tool that can help firms avoid the most serious security threats and uncover online system vulnerabilities before hackers do is the Intruder, a cloud-based vulnerability scanner. It finds and prioritizes cybersecurity weaknesses.
The goal of the intruder vulnerability scanner is to eliminate or greatly decrease the likelihood of any cybersecurity data breaches.
Time is literally saved by Intruder since it proactively scans for new threats and provides a special threat interpretation system that makes vulnerability management straightforward.
Companies without the manpower or funds to sustain an effective vulnerability management program can benefit from this tool’s features.
Features
- Intruder’s surround scanning tool allows users sift data and get context-based results.
- Cybercriminals target your websites, computers, cloud services, and endpoint devices for public and private use.
- You may focus on what matters as Intruder analyzes raw data from top search engines.
- Security teams can assess, monitor, and respond to new threats using the intruder’s evolving threat scanner.
| What is Good? | What Could Be Better? |
|---|---|
| New vulnerability detection. | Reports might include more information. |
| It continuously monitors the attack surface to ensure your security. | The internal agent distribution process is still largely manual. |
| Intruders are used to check the various server fleets for external vulnerabilities. | Unable to search deeper into a target’s file system for data that might be attacked. |
| Internal devices minimize performance degradation with small footprints. |
Price
You can get a free trial and personalized demo from here.
7 – Aircrack – Ng

If you’re looking for a complete suite of Ethical Hacking Tools to evaluate WiFi network security and break Windows WEP and WPA-PSK, go no further than Aircrack-Ng.
While WPA PSK and WPA2 are cracked using brute-force attacks on known passwords, WEP is cracked via statistical analysis.
Although Linux is its primary operating system, it is also compatible with Windows, macOS, Solaris, NetBSD, OpenBSD, FreeBSD, and even eComStation 2.
Among the many topics covered are testing, monitoring, attacking, and cracking as they pertain to wifi security.
Aircrack and similar tools are essential for penetration testers.
Heavy scripting is feasible because all tools are command-line based.
Features
- Aircrack-ng targets clients, not Access Points, and is configurable.
- It breaks WEP without certified clients.
- It lets you make graphs of wireless networks.
- It breaks wireless security regulations.
| What is Good? | What Could Be Better? |
|---|---|
| Comes with a pre-installed Kali Linux. | No graphical user interface |
| capable of breaking wireless network encryption. | Excels at cracking WEP encryption, which is no longer used on wireless systems. |
| Versions of Windows as well as Unix, Linux, and macOS are available | The WPA-TKP utilities don’t work. |
| Ability to capture and export data packets. |
Price
You can get a free trial and personalized demo from here.
8- Nessus

The Nessus tool, created by Tenable, Inc., is an ethical hacking and security scanner that may be used remotely.
is utilized during penetration testing, vulnerability assessments, and malicious attack simulations.
If a computer scan finds any security holes that would allow hackers to get access to other computers on your network, you will receive a notification.
With the help of Nessus’s point-in-time evaluations, security experts can readily find and fix vulnerabilities, such as security flaws and misconfigurations, across a wide range of operating systems.
Administrators of any machine with an internet connection can benefit greatly from using Nessus to help protect their domains from common viruses and hackers that take advantage of simple security holes.
Unlike competing scanners, Nessus does not guess at your server’s settings, which means it will not miss security holes that other scanners could overlook.
Features
- Port checkers compare web server security to DNS and SSH.
- It supports JavaScript, AJAX, ASP, ASP.NET, PHP, Ruby, JRun, CGI, and all major web technologies.
- Finding low-rights directories.
- A vulnerability editor lets one tweak or create exploit strikes.
| What is Good? | What Could Be Better? |
|---|---|
| The results of the scan can be reported in various formats, plain text, XML, and HTML. | Scanning large data sets and applications takes time. |
| Assigning the proper score to vulnerabilities that have been found. | Reports could use an upgrade. |
| Identifying known vulnerabilities. | We can not disable the plugin inside the plugin groups. |
| We can track down any critical patches that are lacking for workstations or servers. | When you scan deeply, you use more resources. |
Price
You can get a free trial and personalized demo from here.
9 – Acunetix
One tool developed to combat the increase in application layer threats is Acunetix Web Vulnerability Scanner, which tests the security of web applications.
Its intended use is to aid web developers and network administrators in protecting servers and apps against a variety of dangers.
In order to check the safety of a website, Acunetix WVS launches a battery of attacks.
Once vulnerabilities have been found, it will clearly report them and even suggest ways to remedy them.
The program lets you set a goal for the number of webpages you want to categorize.
Next, you’ll need to input some options, like the scan speed and your login details.
Acunetix is able to detect over seven thousand vulnerabilities by utilizing a hybrid approach that combines DAST and IAST (Interactive Application Security Testing) scanning.
The three pillars upon which Acunetix stands are (1) Find, (2) Fix, and (3) Prevent.
Features
- Completely checks for OWASP Top 10, SQL attack, XSS, and other security issues.
- Interactive application security testing (IAST) improves accuracy and reduces false hits.
- Uses various development tools, issue trackers, and CI/CD procedures without issues.
- Prepares PCI DSS, HIPAA, and GDPR compliance reports for the company.
- In addition to web application vulnerability scanning, it evaluates network security.
| What is Good? | What Could Be Better? |
|---|---|
| Easily relaunch scans on website sections that have been modified. | It is not very good at supporting multiple endpoints. |
| Supports importing state files from other well-known application testing tools. | Not a lot of scan options to configure. |
| Has additional features built in addition to vulnerability scanning. | Modern enterprise apps have authentication issues when using services and applications with different URLs. |
| The majority of the critical and well-known vulnerabilities are included. |
Price
You can get a free trial and personalized demo from here.
10 – Sqlmap
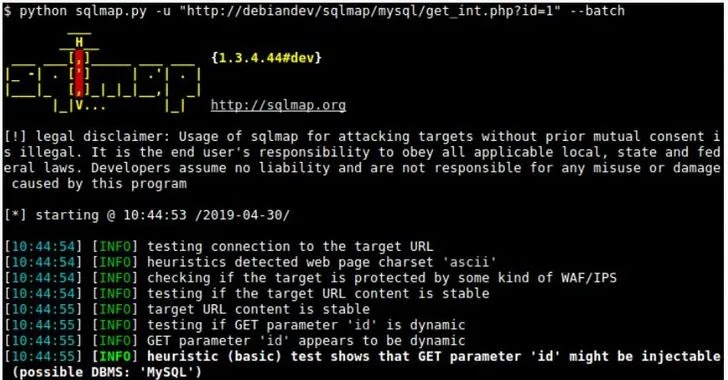
Sqlmap automates the process of discovering and exploiting SQL injection vulnerabilities and manipulating database servers.
It is one of the free and open-source Ethical Hacking Tools built in Python.
All contemporary database systems are compatible with it. This includes Microsoft SQL Server, Oracle, PostgreSQL, MySQL, and PostgreSQL.
The purpose of sqlmap is to identify and exploit web application SQL injection vulnerabilities.
A comprehensive back-end database management system fingerprint, user enumeration, password hash generation, and other options become available to the user if it finds one or more SQL injections on the target server.
The application’s capacity to construct and execute SQL queries is susceptible to modification by user input in the presence of a SQL injection vulnerability.
When it comes to web applications, servers, and databases, however, defenders have SQLMap at their disposal for penetration testing.
This technology gives ethical hackers the ability to access servers and databases.
Features
- Users, password hashes, jobs, databases, tables, and columns can be listed.
- Without SQL injection, we can connect to databases directly using DBMS passwords, IP addresses, ports, and database names.
- You can only dump a fixed number of items from each column.
- Detail and adaptability for user adjustments and features.
| What is Good? | What Could Be Better? |
|---|---|
| It has the ability to access the server and automatically detect and use the SQL Injection Vulnerability database. | It generates a good amount of false positives. |
| It supports HTTP protocol basic, digest, NTLM, and Certificate and authentications support. | SQLmap does not have a graphical user interface |
| Password hash formats are automatically recognized, and a dictionary-based cracking method is supported. | Manual confirmation of vulnerability |
Price
You can get a free trial and personalized demo from here.
11 – Angry IP Scanner
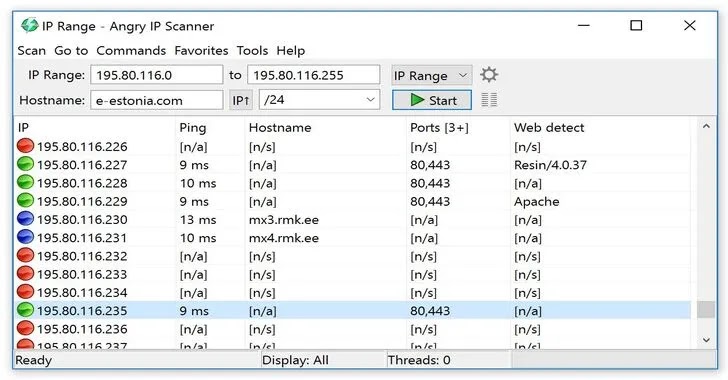
A quick and user-friendly network scanner, Angry IP Scanner is compatible with Windows, Linux, and MAC.
It searches IP addresses and ports and is open-source and works on multiple platforms.
With its high degree of extensibility, it may serve a variety of functions and achieve its primary goal of being useful to network managers.
Without installation, it just checks the availability of all IP addresses by pinging them, and if desired, it may also resolve their hostname, find their MAC address, and scan their ports.
The amount of data collected about each host can be expanded with the use of plugins.
Angry IP Scanner employs a multithreaded method, which means that for each IP address that is scanned, a different thread is created. This is done since performance is absolutely critical for any scanner.
Features
- Finds IP addresses and ports in a network range rapidly.
- All three operating systems—Windows, macOS, and Linux—are supported.
- To narrow scans, users can select IP and port ranges.
- detects open ports, services, and protocols on network objects.
- Gets hostname, workgroup, and logged-in user data from NetBIOS.
| What is Good? | What Could Be Better? |
|---|---|
| Pings and scans a large number of IP addresses. | It’s easy to use but thorough to operate an Angry IP scanner. |
| Users must manually enter the IP address range because there is no predefined one for scanning. | Does not provide the maximum amount of detailed information. |
| Runs on Linux, Windows, Mac OS X, and other platforms. | Users must manually enter the IP address range because there is no predefined IP address range for scanning. |
Price
You can get a free trial and personalized demo from here.
12 – Qualys Guard

The Qualys Guard is a web-based vulnerability management and network security tool provided by Qualys, Inc., the industry leader in the delivery of vulnerability management services as a web service based on a SaaS model.
This vulnerability management software includes app scanning and security, network device mapping and detection, vulnerability prioritization schedule and remediation, and other features.
Qualys appliances handle internal scans and communicate with the cloud-based system afterward.
By providing crucial security intelligence on demand, the Qualys Cloud platform’s integrated apps assist organizations in streamlining security operations and lowering the cost of security compliance.
You can strengthen your detection and response capabilities and assemble your security and compliance stack with integrated, centrally managed apps.
Features
- Finds and prioritizes network, endpoint, and web app vulnerabilities.
- immediately lists all IT assets.
- Monitors security posture in real time to identify new threats.
- Configurations are checked for PCI DSS, HIPAA, and other business compliance.
| What is Good? | What Could Be Better? |
|---|---|
| dashboard for a security posture that is unified. | Some of the tasks involved in choosing sensors can be automated. |
| Detailed information on the findings, including the cause, impact, risk, and potential solutions. | There should be an Excel or CSV reporting option available. |
| Really good and up-to-date vulnerability database. | There are many packages to click through, and the navigation is pretty complicated. |
| The same management interface can accommodate the addition of additional modules. | The graphical user interface could be made a little simpler. |
Price
You can get a free trial and personalized demo from here.
13 – Invicti
To find security flaws in your online apps, you can use Invicti, an automated tool for evaluating application security or scanning web apps for vulnerabilities.
In 2020, Netsparker changed its name to Invicti Security, although it continues to make an online security scanner that can find and exploit vulnerabilities effectively.
As a result of Invicti, DAST, IAST, and SCA are formed. Websites and APIs can be scanned for security concerns.
It detects vulnerabilities in online applications, such as SQL injections, Cross-Site Scripting (XSS), path traversal, and unvalidated redirects in APIs and web apps.
It is capable of finding security flaws in contemporary apps regardless of their architecture or platform.
Whether the scan came up with a false positive or not, Invicti will show that an exploit is there when it finds a vulnerability.
Features
- employs advanced scanning to pinpoint security vulnerabilities.
- Automatically detects SQL attack, XSS, CSRF, and other vulnerabilities.
- Showing exploitable vulnerabilities reduces false alarms.
- This tool checks RESTful APIs for vulnerabilities.
| What is Good? | What Could Be Better? |
|---|---|
| It has an elaborate mechanism for results. | For end users, the reporting option needs to be improved. |
| Many security firms scan the websites of their clients using Invicti. | Currently, Invicti is only compatible with well-known systems, such as Java, and does not integrate with all systems. |
| With some licensing restrictions, this tool is available in both web and desktop versions. | No documentation is provided for using the product. |
| It is very user-friendly, has an organized user interface, and keeps track of all the various scans we have set up in a clean visual. |
Price
You can get a free trial and personalized demo from here.
14 – Open Vas
One thorough vulnerability assessment tool that may find security flaws in any server or network device is the Open Vulnerability Assessment System (Open VAS) scanner.
The Greenbone Enterprise appliances run an extensive feed of vulnerability tests (VTs) using this comprehensive scan engine.
It has a powerful internal programming language that allows it to execute any vulnerability test, leverage a wide range of industrial and internet protocols (both low- and high-level), and conduct authenticated and unauthenticated testing.
The client-side scan configuration and report viewing are both accessible through an interface for the network administrator.
Using your infrastructure, OpenVas can find and classify any vulnerabilities, as well as the risk they represent and how to fix them.
Features
- Full vulnerability checks find issues with system and network security.
- This free, open-source technology allows the community modify it.
- Monitors hosts, services, open ports, and other network assets.
- checks identity using a wide library of known security flaws.
- Set and update rules and scan setups.
| What is Good? | What Could Be Better? |
|---|---|
| It performs comprehensive security testing of an IP address. | Does not offer policy management |
| OpenVAS frequently updates its scan engine. | Due to automation, web scanning occasionally leaves very basic vulnerabilities. |
| Around 26,000 Common Vulnerabilities and Exposures (CVE) are covered. | Less Operating System Supportability |
| OpenVAS supports a wide variety of plugins, giving users more flexibility when conducting security assessments. |
Price
You can get a free trial and personalized demo from here.
15 – Ettercap
Supporting man-in-the-middle attacks on networks, Ettercap is an open-source and free program.
Computer network protocols and security audits are two areas that can benefit from its usage.
Data can also be redirected and altered in real-time through virtual means.
It is capable of capturing packets and re-encoding them for use on the network.
Active and passive protocol dissection is supported, and it comes with a plethora of tools for network and host investigation.
With Ettercap, you can actively eavesdrop on many major protocols, intercept traffic on a specific portion of a network, and even steal passwords.
Because it allows for inspection of network traffic, ettercap is most often used to build up man-in-the-middle attacks utilizing ARP poisoning.
Itercap is an essential tool for any ethical hacker or penetration tester.
Features
- Intercepting and studying networks using man-in-the-middle approaches.
- You may monitor and alter ARP, DNS, HTTP, and other protocols.
- Active and passive scanning are used for network espionage.
- It sometimes decrypts SSL/TLS data.
- Features can be added and adjusted via plugins.
| What is Good? | What Could Be Better? |
|---|---|
| Both the command line interface and the graphical user interface (UI) of Ettercap are nice. | It is not compatible with Windows 10 or 64-bit architecture. |
| It supports plug-ins so that additional plugins can be added to expand the features. | The software’s source compilation needs a number of dependencies and developer libraries to work properly. |
| Provides strategies for isolating particular endpoints. | Ettercap only works if it is already installed on a computer connected to the target network. |
| Because of the variety of features, it is simple for an ethical hacker to conduct network reconnaissance before launching a session hijacking attack. |
Demo video
Price
You can get a free trial and personalized demo from here.
Frequently Asked Questions
Exploiting or exposing a website in order to find its weaknesses is an example of ethical hacking.
After that, inform the appropriate party of your findings so they can address the vulnerabilities.
External testing involves looking for flaws when an outsider tries to hack into a system or an organization.
This kind of testing looks for weaknesses in email servers, issues with third-party applications, or potentially misconfigured firewalls.
Internal testing searches for potential problems within a company, frequently ones that are caused by human error and make use of
Weak passwords, susceptibility to phishing and social engineering scams, and a failure to update systems and devices can all contribute to this.
The field is very active and requires continuous research.
To be a successful investigator, you must constantly read published work from colleagues and pick up new techniques.
Inconsistency in quality, The cyber industry is home to a large number of ethical hackers and businesses that provide services related to penetration testing and ethical hacking.
It can be difficult for businesses to sort through the noise and find quality providers.
Use of automated tools too frequently Ethical hacking should be manually led, with the specialist relying on experience and knowledge and only using automated software tools as a last resort.
System disruption brought on by ethical hackers, When providing their ethical hacking services, less skilled ethical hackers are more likely to cause problems and business interruptions.
Also Read
Best Free Penetration Testing Tools
10 Dangerous DNS Attacks Types and The Prevention Measures
Free Forensic Investigation Tools
Bug Bounty Platforms for Every White Hat Hackers
Best Search Engines That You Can Use Instead of Google
Best Free Web Application Penetration Testing Tools
AWS Security Tools to Protect Your Environment and Accounts
SMTP Test Tools to Detect Server Issues & To Test Email Security
Online Penetration Testing Tools for Reconnaissance and Exploit Search



