Trending Now
Latest Cyber Security news
Hackers Infiltrated 9-days Within UnitedHealth Network Before Ransomware Attack
Andrew Witty, CEO of UnitedHealth Group, detailed a sophisticated ransomware attack on Change Healthcare, a key component of the UnitedHealth network.
The cybercriminals, identifying...
Malware Cuckoo – Previously Unknown Infosteler Spyware Steals Data From MacOS
Security researchers have uncovered a previously undetected malware threat for macOS that exhibits characteristics of both an infostealer and spyware. Dubbed "Cuckoo" after the...
Postman API Testing Platform Flaw Exposes Sensitive Credentials
Truffle Security Co. has recently discovered a major vulnerability in Postman, the widely used API testing platform.
This flaw exposed over 4,000 active credentials,...
Millions of Docker Hub Repositories Found Pushing Malware for Over 5 Years
It has been found that almost one-fifth of the repositories on Docker Hub, a popular platform for developers to store and share containerized applications,...
Investigating Two TeamCity Authentication Bypass Vulnerabilities
Vulnerability exploits are the third most common way that cybercriminals gain access to target organizations, surpassed only by credential stealing and phishing in 2023....
Threat Actors Claiming of 0-Day Vulnerability in Zyxel VPN Device
Threat actors have claimed to have discovered a 0-day vulnerability in Zyxel VPN devices.
This revelation was made public through a tweet by the...
Muddling Meerkat Using DNS As A Powerful Weapon For Sophistication
Hackers exploit DNS vulnerabilities to redirect users to malicious websites, launch distributed denial-of-service (DDoS) attacks by overwhelming DNS servers, and manipulate domain resolutions to...
Pathfinder – New Attack Steals Sensitive Data From Modern Processors
Microarchitectural side-channel attacks misuse shared processor state to transmit information between security domains.
Although they can be used in isolation, they are frequently employed as...
Beware of New Android Trojan That Executes Malicious Commands on Your Phone
Cybersecurity researchers at XLab have uncovered a new Android malware strain called "Wpeeper."
This sophisticated backdoor Trojan has been designed to infiltrate Android systems and...
Authorities Seized Platform Used For Paid DDoS
On April 17, 2024, a joint effort between the Dresden Public Prosecutor’s Office and the Cybercrime Competence Center of the Saxony State Criminal Police...
Top 10
Most Important Python Security Tools for Ethical Hackers & Penetration Testers 2024
There are a variety of Python security tools are using in the cybersecurity industries and python is one of the widely used programming languages...
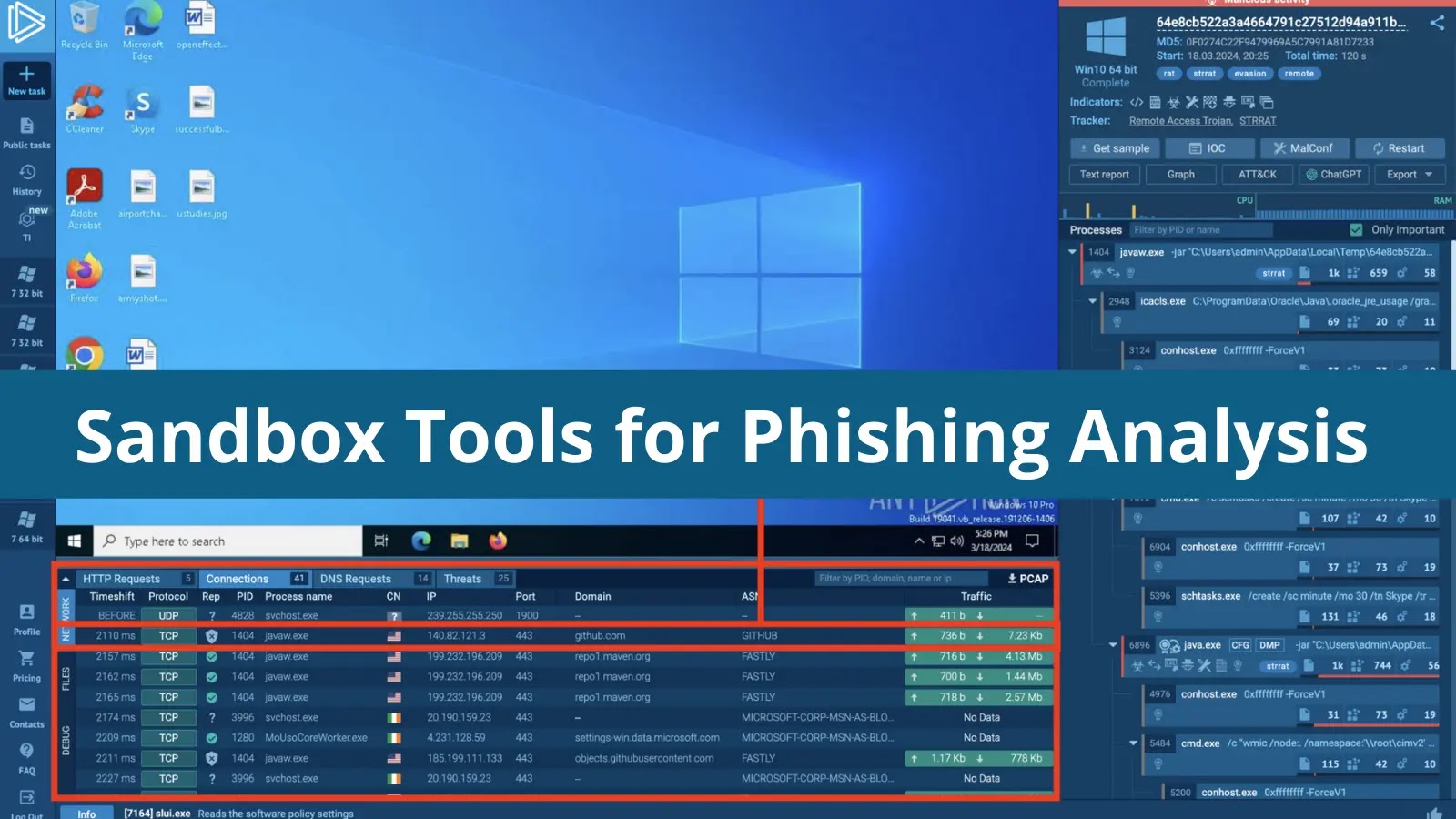
5 Sandbox Tools for Phishing Analysis in 2024
There is a wide variety of solutions one can use to investigate phishing attacks. Yet, in most cases, analysts can do with just one,...
NSA Releases Top 10 Cloud Security Mitigation Strategies – 2024
NSA and CISA jointly released "Top 10 Cloud Security Mitigation Strategies" to advise cloud users on critical security practices for migrating data.
The National Security...
10 Best Network Security Solutions for Chief Security Officer to Consider – 2024
Any place that stores sensitive information is a prime target for hackers worldwide, and government institutes hold the most critical amount of data about...
10 Best Network Security Solutions for Enterprise – 2024
Implementing robust network security solutions for enterprises is crucial to protect sensitive data, maintain privacy, and ensure business continuity.
Given the complexity and scale...
11 Best Web Security Scanners For Vulnerability Scanning – 2024
Web Security Scanners: The world is moving towards digitalization; from small to large, every business has a website running to showcase its services, and...
12 Best Vulnerability Management Tools 2024
Vulnerability Management Tools play a significant role in detecting, analyzing, and patching vulnerabilities in web and network-based applications.
Vulnerability, risk, and threat are the...
Best AWS Network Access Security Solutions – 2024
AWS (Amazon Web Services) network access refers to the methods and services that allow users and applications to connect to AWS resources, services, and...
6 Best Free Malware Analysis Tools to Break Down the Malware Samples – 2024
The malware analysis tools simply allow us to quickly and effectively determine what actions a threat takes in the system.
This method easily collects...
10 Best Automatic WiFi Security Providers – 2024
When looking for the best automatic WiFi security providers in 2024, it's essential to focus on services that offer robust encryption, reliability, and a...
Zero-Days
What is
- All
- Acquisition
- Android
- Apple
- Automotive
- Botnet
- Bug Bounty
- Cisco
- cloud
- computer Security
- cryptocurrency
- Cyber AI
- Cyber Attack
- Cyber Security
- Cyber Security News
- Cyber Security Research
- Cyber security Resources
- Darknet
- Data Beach
- Data Breaches
- Data protection
- Data Theft
- DDOS
- Defender ATP
- Digital Forensics
- DNS Attacks
- Endpoint Security
- Exploit
- Featured
- FireFox
- Firewall
- Hacking Tools
- Hacks
- Healthcare
- Information Security
- iOS
- IoT
- Kali Linux
- Lawsuit
- Linux
- macOS
- Malware
- Microsoft
- Network Security
- New Post
- News
- Passwords
- Penetration Testing
- Phishing
- Press Release
- Privacy
- Proxy
- Python
- Ransomware
- Routers
- SCAM
- Security Updates
- Sharepoint
- Spoofing
- SSL
- Technology
- Technology
- Threats
- Top 10
- Top Global News
- Tor
- Training
- VPN
- Vulnerability
- Vulnerability Roundup
- Web Application
- Web Security
- what is
- Wi-Fi
- Windows
- Wireshark
- Wordpress
- XDR
- Zero-Day
More




.webp)







.webp)






-1.webp)






.png)




