Cybersecurity researchers at XLab have uncovered a new Android malware strain called “Wpeeper.”
This sophisticated backdoor Trojan has been designed to infiltrate Android systems and execute a wide range of malicious commands, posing a significant threat to unsuspecting users.
Wpeeper’s distribution strategy is particularly cunning.
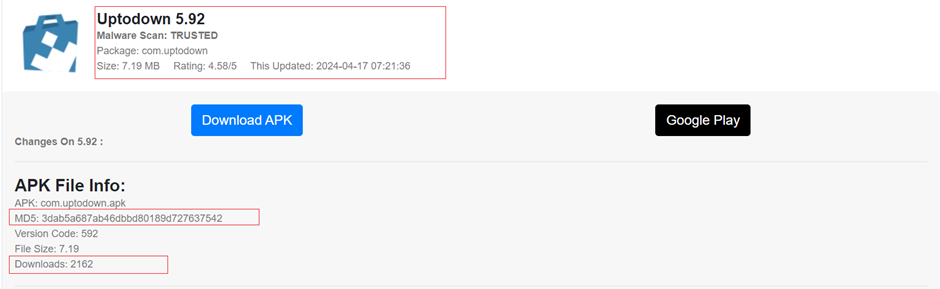
The malware is being distributed through repackaged applications on the UPtodown app store, a popular third-party platform similar to Google Play.
By embedding a small code snippet into regular APKs, the attackers have managed to bypass antivirus detection.
The modified APKs currently show zero detections on VirusTotal.
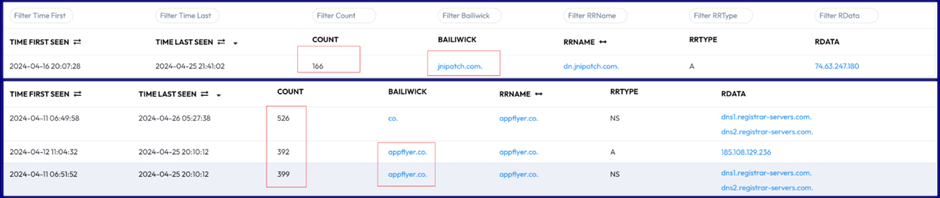
The malware’s network operations are equally sophisticated, featuring a multi-level command-and-control (C2) architecture that relies on compromised WordPress sites as relay servers.
Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide
This approach effectively conceals the true C2 server, making it more challenging for security researchers and authorities to track and disrupt the operation.
Extensive Capabilities and Encrypted Commands
Wpeeper is a typical backdoor Trojan for Android systems, supporting many malicious functions.
These include collecting sensitive device information, managing files and directories, uploading and downloading data, and executing arbitrary commands on the infected device.
The most notable feature of Wpeeper is its use of encryption and digital signatures to protect its network traffic and commands.
All communications between the malware and the C2 servers are encrypted using AES, and an elliptic curve signature accompanies the commands to prevent unauthorized takeover or tampering.
Abrupt Halt and Potential Larger Scheme
Researchers at XLab have been closely monitoring Wpeeper’s activities and observed an abrupt halt in the campaign on April 22.
Integrate ANY.RUN in Your Company for Effective Malware Analysis
Are you from SOC, Threat Research, or DFIR departments? If so, you can join an online community of 400,000 independent security researchers:
- Real-time Detection
- Interactive Malware Analysis
- Easy to Learn by New Security Team members
- Get detailed reports with maximum data
- Set Up Virtual Machine in Linux & all Windows OS Versions
- Interact with Malware Safely
If you want to test all these features now with completely free access to the sandbox:
The C2 servers and downloaders suddenly stopped providing services, leading the researchers to suspect that this could be part of a larger strategic move by the attackers.
One possible explanation is that the attackers may have intentionally stopped the network activity to allow the repackaged APKs to maintain their “innocent” status in the eyes of antivirus software.
This could enable the malware to increase its installation numbers and reveal its true capabilities later, potentially catching security teams off guard.
While XLab does not have direct data on the Wpeeper distribution scale, their analysis of Google and Passive DNS (PDNS) results suggests that the infection is at the thousand level without widespread propagation.
However, the researchers emphasize that the threat remains ongoing, as the relevant samples continue to evade detection by security firms.wpeeper_google.png
Detailed Analysis of Wpeeper’s Functionality
The researchers have thoroughly analyzed Wpeeper’s functionality, shedding light on its inner workings.
Family: Wpeeper
MD5: 8e28f482dab8c52864b0a73c3c5c7337
Magic: ELF 64-bit LSB pie executable, ARM aarch64, version 1 (SYSV), dynamically linked, interpreter /system/bin/linker64, BuildID[sha1]=9fa32612558fab9480496f6b31fa5426ae8885d4, stripped
Packer: None
Obtaining Command-and-Control Servers
Wpeeper uses two methods to populate its list of C2 servers.
The first is by decoding the embedded C2 servers within the malware sample, while the second is by reading and decrypting the “store.lock” file, which contains additional C2 server information and other configuration data.
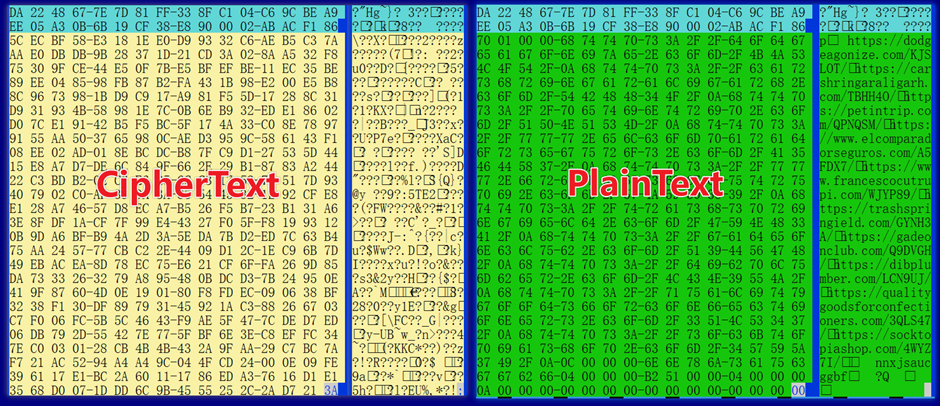
Wpeeper employs the libcurl library to construct POST requests for communicating with the C2 servers.
The malware uses the Cookie and Session fields in the HTTP headers to differentiate between different types of requests, such as beacons, command requests, and result uploads.
struct c2info
{
uint32 lenOfC2;
char[lenOfC2] C2s;
uint32 lenOfCookie;
char[lenOfCookie] cookie;
uint32 flag;
uint32 id;
uint32 flag;
uint32 interval;
}
The network traffic is further protected by the use of AES encryption and elliptic curve digital signatures, ensuring the integrity and confidentiality of the communications.Command Execution and Supported Functionalities
Wpeeper supports 13 different commands, ranging from collecting device information and package lists to downloading and executing arbitrary files.
| CMD | FUNCTION |
| 1 | collect device info |
| 2 | collect pkg list |
| 3 | update c2 |
| 4 | set interval |
| 5 | update pubkey |
| 6 | download |
| 7 | collect arbitrary file info |
| 8 | collect arbitrary dir info |
| 9 | exec arbitrary cmd via shell |
| 10 | download from C2 , then exec |
| 11 | update and exec |
| 12 | self-destruction |
| 13 | download from arbitrary URL, then exec |
The researchers have provided detailed information on the various commands and their corresponding functionalities.
Through their command tracking and analysis, the researchers have gained valuable insights into the attackers’ tactics and the overall structure of the Wpeeper operation.
The researchers have identified 45 C2 servers used by Wpeeper, most of which are compromised WordPress sites serving as C2 redirectors.
This multi-layered approach helps shield the true C2 server from detection while also introducing potential reliability issues if the compromised sites are discovered and taken down.
Among the nine hardcoded C2 servers, the researchers believe that one, tartarcusp.com, is likely owned by the attackers themselves, providing an additional layer of control and resilience to the operation.
The researchers at XLab have provided a comprehensive overview of the Wpeeper Android Trojan, highlighting its sophisticated design, extensive capabilities, and the potential larger scheme behind the attackers’ actions.
They emphasize the ongoing nature of the threat and invite peers with unique perspectives and administrators of affected websites to provide further clues and insights.
As the cybersecurity landscape continues to evolve, users, security professionals, and researchers must remain vigilant and collaborate in the fight against emerging threats like Wpeeper.
By sharing information and working together, the security community can better protect Android users from the dangers posed by this sophisticated malware.
IOCs
MD5
APK
3dab5a687ab46dbbd80189d727637542
ELF
003577a70748ab4ed18af5aecbd0b529
32e92509bc4a5e3eb2146fe119c45f55Reporter
https://eamdomai.com/e?token=Tp5D1nRiu3rFOaCbT4PVcewqIhqbQspd8/3550AI/b1MMJttn+xr4oEFJiGx1bCZztteCi5dG1gYFlNTL0Fp8UaMxROCw4cr225ENjOCmT8oQUyMTjjuTo10fAuFsz9jDownloader
https://appflyer.co/downloads/latest/device/android/
https://dn.jnipatch.com/downloads/latest/device/androidC2 Redirectors
Hardcoded
https://tartarcusp.com/BZRAWE/
https://www.chasinglydie.com/7V5QT0/
https://www.civitize.com/0SA67H/
https://wyattotero.com/AQVLLY/
https://web.rtekno.com/5XPOS2/
https://dermocuidado.com/8QSCZP/
https://ocalacommercialconstruction.com/WXFHF6/
https://scatsexo.com/NVZ4L0/
https://snipsnack.com/T8Q2BN/
New
https://4devsolutions.com/4NUAK1/
https://atba3li.com/Z99QQ6/
https://avsecretarial.com/PYWDEL/
https://barbeariadomarfim.com/BN2TTO/
https://beanblisscafe.com/MX1OAS/
https://carloadspry.com/SJI4C1/
https://carshringaraligarh.com/TBHH4O/
https://coexisthedge.com/ZF57OA/
https://dibplumber.com/LCN9UJ/
https://dodgeagonize.com/KJSLOT/
https://essentialelearning.com/EVSKOT/
https://focusframephoto.com/1J10V9/
https://fontshown.com/4D69BN/
https://gadeonclub.com/Q9DVGH/
https://hhfus.com/CUGCCO/
https://kiwisnowman.com/DC4O03/
https://masterlogisticsfzco.com/5CBSYC/
https://mrscanology.com/8GVHT3/
https://naroyaldiamonds.com/WZJ236/
https://nt-riccotech.com/Q4LQKN/
https://nutrivital-in.com/7DB9BC/
https://petintrip.com/QPNQSM/
https://qualitygoodsforconfectioners.com/3QLS47/
https://rastellimeeting.com/9Q4GOM/
https://schatzrestaurant.com/J2WMA6/
https://socktopiashop.com/4WYZ7I/
https://speedyrent-sa.com/AIOFB2/
https://stilesmcgraw.com/1WN2BH/
https://toubainfo.com/G1ACF0/
https://trashspringield.com/GYNH3A/
https://vaticanojoyas.com/R5Q7G4/
https://wendyllc.com/QD8490/
https://www.cureoscitystaging.com/YKUCU8/
https://www.elcomparadorseguros.com/A5FDX7/
https://www.francescocutrupi.com/WJYP89/
https://www.yitaichi.com/K7ODU6/Combat Sophisticated Email Threats With AI-Powered Email Security Tool -> Try Free Demo


.webp)



