Network security for Software as a Service (SaaS) requires a combination of rules, procedures, and technologies to ensure the confidentiality, integrity, and availability of SaaS-provided data and services.
As-a-Service Security (SaaS) refers to a cloud-based methodology for delivering security services over the Internet, specifically in the context of network security.
Businesses increasingly use security services provided by third-party providers as an alternative to building and operating hardware and software on-premises.
Some of the services offered include anti-malware and firewall protection, intrusion detection, and security event management.
SaaS provides businesses with up-to-date security, lowers the cost of infrastructure, and allows for expansion.
Without requiring much interaction from the user, this architecture ensures that security measures are continually updated in response to the growing threat landscape.
Table of Contents
Why is SaaS Security so important?
Challenges in Securing SaaS Platforms
SaaS Security Best Practices
Best Network Security Vendors for SaaS Features
Best Network Security Vendors for SaaS
1. Perimeter 81
2. Palo Alto Networks
3. Fortinet
4. Symantec
5. Qualys
6. McAfee
7. Okta
8. Sophos
9. Netskope
10. Check Point
Conclusion
FAQ
Why is SaaS security so important?
SaaS security is crucial since many businesses now run on cloud-based software. Despite the convenience and scalability, these systems might leave users vulnerable.
If sensitive data is compromised in a SaaS application due to unauthorized access, a data breach, or another cyber incident, it could lead to financial losses, regulatory penalties, and brand harm.
A solid SaaS security system is more important when protecting your business, stakeholders, and users’ confidence.
Without careful SaaS security measures, businesses risk not only data breaches but also failing to meet international regulations, which carries its own complications.
Challenges in Securing SaaS Platforms
| Multi-tenancy: | If necessary isolation isn’t maintained, the reality that SaaS platforms host several clients on the same resources might result in data leakage or breaches. |
| Data Privacy: | It might be difficult to guarantee data security and compliance with widely varied worldwide requirements, such as GDPR. |
| Access Control: | It’s essential to restrict access to sensitive information and features to only those who need it, but it cannot be easy to manage permissions. |
| Shadow IT: | Unauthorized use of SaaS applications by employees can compromise a company’s network without the knowledge of IT personnel. |
| Data Residency: | It can be challenging to comply with data protection rules worldwide and ensure data is stored in appropriate locations. |
| Loss of Control: | When companies use SaaS from outside vendors, they give up some control over the system’s security. |
| End-Point Security: | With consumers using SaaS platforms from a wide variety of devices, it is always a challenge to keep each endpoint secure. |
| Account Hijacking: | Cyberattacks, such as phishing, can result in stolen information or the misuse of sensitive accounts. |
| Inconsistent Security Policies: | Using a wide variety of SaaS products could make your network vulnerable due to inconsistencies in their security measures. |
SaaS Security Best Practices
- Multi-Factor Authentication (MFA): Multi-factor authentication can reduce the risk of unauthorized entry.
- Single Sign-On (SSO): Minimize the attack surface and the possibility of users losing their passwords by centralizing user authentication.
Data Encryption:
- In-Transit: Data communication between client and server should be encrypted using protocols such as TLS.
- At-Rest: Ensure all your databases and other data storage locations use encryption.
Regular Security Audits and Assessments:
- Check the security measures and configurations regularly.
- Use a penetration testing service to find security flaws.
Data Backup and Recovery:
- Establish fully automated backup systems.
- Make sure you’re ready for any incident.
Endpoint Security:
- Make sure all devices used to access the SaaS app are protected.
- Always keep your hardware up to date and patched.
API Security:
- You can keep application interfaces safe from attacks using API gateways and regular security testing.
Network Security:
- Protect your network using firewalls, IDS/IPS, and secure protocols.
Monitoring and Alerting:
- Logs and records of transactions should be monitored constantly.
- Set up instant notifications whenever anything suspicious occurs.
Educate Employees:
- Maintain a consistent schedule of training on security best practices.
- Increase everyone’s awareness of security issues.
Vendor Management:
- Ensure that all external service providers observe severe safety measures.
- Vendor security should be reviewed and evaluated often.
Best Network Security Vendors for SaaS Features
| Best Network Security Vendors for SaaS | Features |
|---|---|
| 1. Perimeter 81 | Safe access from afar Access to a network without trust Authentication with Multiple Factors Adding the cloud Perimeter Set by Software Management from one place |
| 2. Palo Alto Networks | Firewall of the Future Stopping Threats Cleaning up URLs In charge of applications Safety of the Network Cloud Safety |
| 3. Fortinet | The FortiGate Firewall Threat Intelligence from FortiGuard Web Application Firewall from FortiWeb The FortiSandbox Endpoint Security for FortiClient Management in one place with FortiManager |
| 4. Symantec | Stopping Data Loss Safe Web Gateway Managing Identity and Access Keeping track of security information and events Data encryption and safety |
| 5. Qualys | Taking care of vulnerabilities Monitoring All the Time Policy Follow-Up Safety from Threats Questionnaire for Assessing Security Inventory of Assets |
| 6. McAfee | Stopping Data Loss Keeping track of security information and events Guarding the web Email Safety Management of Identity and Access |
| 7. Okta | One-Time Sign-On Authentication with Multiple Factors The Universal Directory Managing the lifecycle Management of API Access Real-time authentication |
| 8. Sophos | Guarding the web Safety for wireless Using encryption Server Safety Safety for wireless |
| 9. Netskope | Taking Care of Cloud Security Protect against insider threats Service Edge for Secure Access Management of Identity and Access Safety for APIs |
| 10. Check Point | Safety of the Network Mobile Safety Knowing Yourself Endpoint Safety In charge of security Zero-Day Protection from SandBlast |
Best Network Security Solutions for SaaS
- Perimeter 81
- Palo Alto Networks
- Fortinet
- Symantec
- Qualys
- McAfee
- Okta
- Sophos
- Netskope
- Check Point
1. Perimeter 81
.webp)
Whether your resources are on-premises or hosted in the cloud, with Perimeter 81 you can see them all and get safe, fast remote access through local gateways.
The most popular cloud services, including Microsoft Azure, Google Cloud, and Amazon Web Services (AWS), can be integrated without any fuss.
Establish role-and device-based, adaptable access controls. Regardless of the setting, you will be able to accomplish thorough monitoring and cost-effective access management.
Use a uniform collection of networking and security solutions to simplify your toolbox and streamline your operations. You may quickly modify the traffic rules and access regulations to accommodate your growing business.
With Perimeter 81, a Secure Access Service Edge solution, you can expect top-notch speed, seamless networking, and top-notch security.
It works wonderfully for multinational technology firms that have dispersed employees and resources.
By implementing measures such as visibility, access control, activity logging, and encryption, you may easily achieve SOC 2 Type 2 and ISO 27001/2 compliance.
Features
- Digital security tools keep people safe from digital risks by blocking dangerous websites.
- With Perimeter 81, workers can safely connect their phones and tablets to the network.
- Its many server sites give users around the world low-latency connectivity and backups.
- Reporting and auditing tools are built into the software to meet compliance needs.
| What is Good? | What Could Be Better? |
|---|---|
| Secure data transmission. | Limited control over SaaS data. |
| Compliance with data privacy regulations. | VPN latency issues. |
| Fine-grained access permissions. | |
| Perimeter 81 usually provides customer support, ensuring availability. |
Perimeter 81 – Trial / Demo
2. Palo Alto Networks
.webp)
In the realm of software as a service applications, App-ID technology allows for constant discovery, classification, and control. This ever-changing procedure is present throughout the whole company and affects all cloud apps.
Assuring compliance across a wide range of contemporary communication technologies and protecting sensitive data, it forms the foundation of cloud business DLP.
Use the vast API coverage of SaaS apps, like Microsoft 365, SFDC, Box, and many more, including popular ones like Slack, Jira, Teams, and
Whether you’re in an authorized or unauthorized SaaS environment, this solution is great at stopping new malware and zero-day attacks.
By consolidating SASE, CASB, and DLP into a single cloud-based dashboard, we can streamline operations and provide a fully integrated security solution.
Take control of your company’s security and data protection from a single, convenient spot.
In addition, it streamlines the organization’s application discovery, regulation, and control processes, which is in line with the exponential expansion of SaaS applications.
Features
- Keeps IoT gadgets safe on the network.
- Offers tools to find risks and handle security incidents instantly.
- Monitoring and reporting in a thorough way help groups follow the rules.
- Cloud processes and containers are safe with Palo Alto Networks.
- A platform for better security orchestration, automation, and response that makes security operations and incident reaction more efficient.
| What is Good? | What Could Be Better? |
|---|---|
| Prevents unauthorized access. | Costly licensing and hardware. |
| Comprehensive DLP coverage. | Incomplete SaaS app visibility |
| Advanced threat detection. | |
| Deep application visibility and control for accurate security policy administration. | |
Palo Alto Networks – Trial / Demo
3. Fortinet
.webp)
The data that flows into and out of your SaaS apps is continually monitored by the vigilant guardians at Fortinet’s SaaS security Vendors.
These safeguards use state-of-the-art techniques that cybercriminals find ingenious. Among these are priceless nuggets of wisdom about governance and compliance requirements.
With Fortinet’s solutions, enterprises get a clear picture through a single interface, thanks to a unified architecture of SaaS security protocols and principles that cover the entire network.
Using the application programming interfaces (APIs) of SaaS apps, the FortiCASB-SaaS Cloud Access Security Broker service keeps tabs on all of their settings and activities.
All aspects of access control, resource management, configuration, and security protocols are standardised because to this centralized approach’s complete visibility.
It also checks all of your saved files thoroughly, finding malware and APTs quickly, so they can’t spread throughout your network.
Features
- Advanced firewall that stops intrusions, controls applications, and checks SSL traffic.
- Real-time danger updates and global threat intelligence to help stop new attacks as they happen.
- SD-WAN and security make the network work better and keep data safe.
- Sandboxing is a way to look at strange files and threats and put them in a safe place.
- Use cloud-native SASE to protect network access and the cloud.
| What is Good ? | What Could Be Better? |
|---|---|
| SaaS application usage is entirely transparent. | Complex setup and management. |
| Visibility and management of resource use | SaaS app performance impact |
| Complete support for all important SaaS applications | |
| Optimizes network administration with SD-WAN and security. | |
Fortinet – Trial / Demo
4. Symantec
.webp)
As vigilant protectors, Symantec’s network security technologies keep the digital realm reliable and secure.
By integrating state-of-the-art technology with extensive features, Symantec’s Software as a Service (SaaS) network security solution fortifies software environments hosted in the cloud.
To start, by monitoring network traffic in real-time, Symantec’s network security employs cutting-edge threat detection and prevention technologies like intrusion detection and prevention systems (IDPS).
Symantec uses strong encryption and access controls to safeguard data at rest and in transit, ensuring that sensitive information remains secret and that regulatory requirements are met.
The SaaS security vendors from Symantec offer comprehensive security analytics and reporting in addition to being able to integrate with a wide range of SaaS platforms and pre-existing network styles.
By providing clarity on things like network traffic, user behavior, and security incidents, these insights make compliance audits easier and proactive threat mitigation is possible.
Features
- Blocks malware, viruses, and online hazards.
- Complete firewall and identity theft protection online.
- The complete security package includes antivirus, VPN, password manager, and more.
- Protects corporate endpoints against sophisticated malware.
- Protects data and detects threats in cloud environments.
| What is Good? | What Could Be Better? |
|---|---|
| Real-time threat insights. | SaaS app compatibility issues. |
| Data protection and encryption | Resource-intensive scanning |
| Proven threat expertise | |
| Offers customer service around the clock. | |
Symantec – Trial / Demo
5. Qualys
.webp)
Modern, flexible enterprises rely on software as a service (SaaS) tools such as Microsoft Office 365, Google Workspace, Salesforce, and Zoom to keep up with the fast-paced corporate landscape of today.
On the other hand, security teams already dealing with inadequate oversight face additional obstacles due to their growing popularity.
As a comprehensive toolkit, QualysNetwork Solution for SaaS outshines competing SaaS security and posture management solutions.
It uses the power of the Qualys Cloud Platform to streamline and automate the management of software as a service (SaaS) applications, including all of their settings, users, licenses, files, and compliance and security situations.
All of your network’s IT assets, whether they’re in the cloud, on-premises, or accessible via mobile devices, are at your fingertips with Qualys’s expanded reach.
It goes so far as to pinpoint any weak spots and gives you the tools to strengthen your defenses. To strengthen your company’s defenses against SaaS threats, implement QualysNetwork Solution for SaaS.
Features
- Risks to IT security are found and ranked.
- Keeps real-time records of the state of assets and security.
- Automatically applies security fixes to systems that are weak.
- Threat intelligence and research can help protect you from threats and weaknesses.
- Evaluation and reporting of compliance help people follow the rules.
| What is Good? | What Could Be Better? |
|---|---|
| Provides many security and compliance solutions. | Limited dashboard and report customization. |
| Easy deployment and scalability without on-premises hardware. | Users report uneven customer support experiences. |
| Continuously monitors assets and vulnerabilities. | |
| Scales for small and large businesses. | |
Qualys – Trial / Demo
6. McAfee
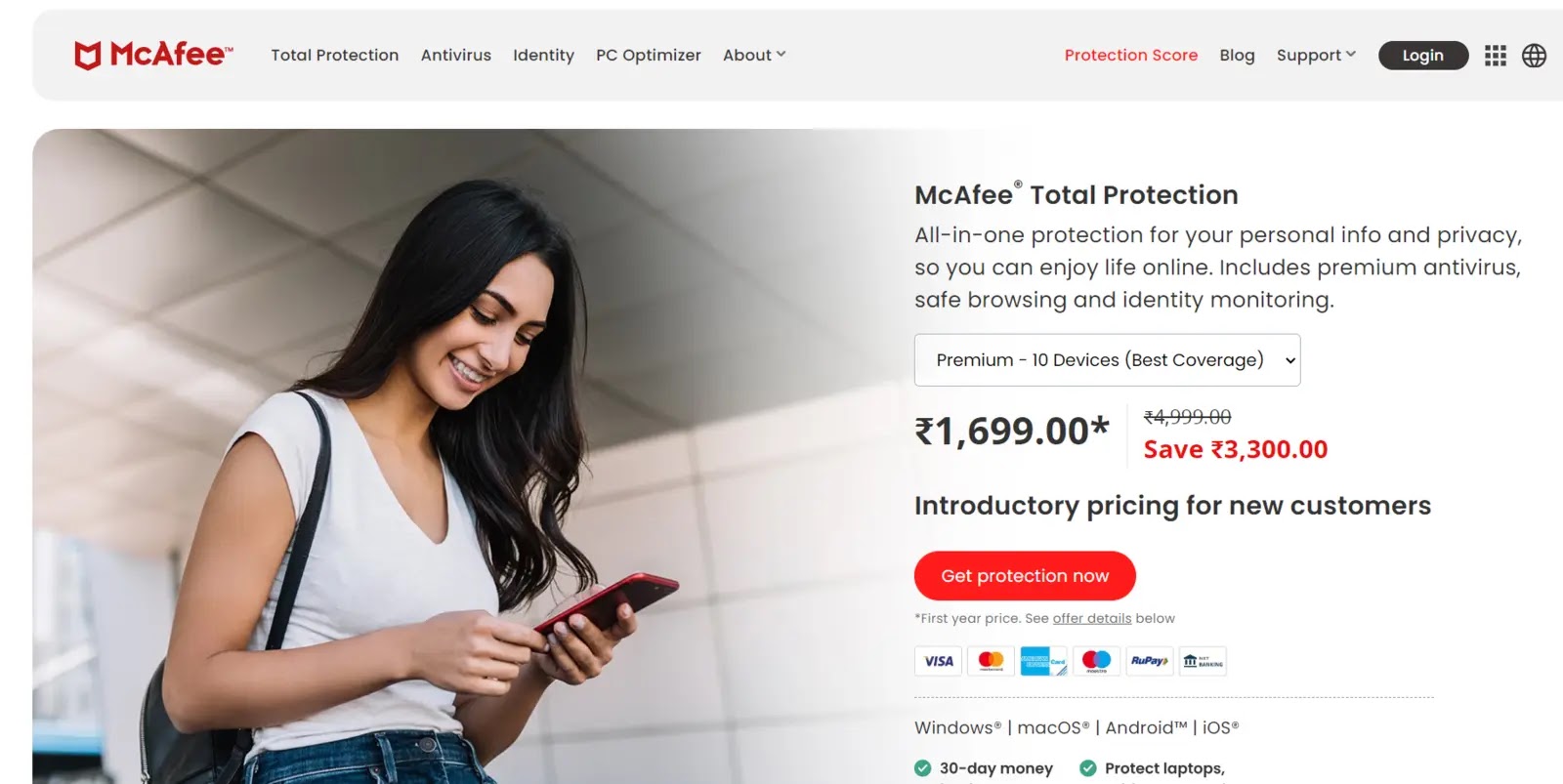
It employs the cloud to secure endpoints, emails, websites, and networks, which simplifies IT processes and reduces expenses.
This ever-changing system is always looking for anything out of the ordinary in the data packets that pass through the network.
Organizations may safeguard critical data and enforce security protocols while moving to the cloud with the help of McAfee’s CASB solution, which gives a transparent view into SaaS usage.
In addition, it fortifies your defenses with features like anti-malware protections, URL filtering, and SSL inspection. Safe access to SaaS applications and protection from phishing attempts are both provided by these products.
Their endpoint security solutions reinforce user devices with features including anti-malware, device control, and antivirus software. When it comes to cybersecurity for software as a service, McAfee’s network security vendors cover all the bases.
You can trust them to keep your sensitive information safe in the cloud while also ensuring that your critical applications and data remain accessible at all times.
Features
- Keeps business computers safe from complex threats and data loss.
- Finds threats and keeps cloud info safe.
- Stops email spam and threats.
- Web data is safe because of real-time scanning and content filtering.
- Keeps an eye on data breaches and unauthorized entry and stops them.
| What is Good? | What Could Be Better? |
|---|---|
| Cloud-native security. | SaaS data privacy concerns |
| Threat intelligence sharing | Frequent false positives. |
| Simplified security operations. | |
| Helps parents keep an eye on and manage their kids’ internet activities | |
McAfee – Trial / Demo
7. Okta
.webp)
You may fortify your present security investments and extend them to the cloud with its help, guaranteeing future preparedness.
With cloud and on-premises security seamlessly integrated, you can administer policies consistently across your whole environment, creating a unified strategy.
The combination of Okta with network security vendors creates a security infrastructure that is policy-driven, easy to use, and reliable, which is good for administrators and end users alike.
No matter where your data, apps, or users are located, they will be protected by the strong security ecosystem that Okta and network security vendors build together.
OKta’s SaaS features include Enterprise Federation, Delegated Administration, Custom Branding, Multi-factor Authentication (MFA), and Pre-built Security Options.
By utilizing Okta, you can effortlessly construct a comprehensive security ecosystem that can adjust to evolving security risks while upholding consistent standards.
Features
- For managing identities and attributes, there should be a single user directory.
- Provisioning, de-provisioning, and updating users are all done automatically.
- Controls access to APIs and microservices safely.
- Adapts identification to the user’s actions and the situation.
- keeps an eye on actions that seem fishy and limits access.
| What is Good? | What Could Be Better? |
|---|---|
| Secure Single Sign-On (SSO) and Adaptive MFA | Limited SaaS protection features |
| Policy-Based Security | Identity spoofing risks. |
| Simplified access through firewalls and VPNs. | |
| Helps meet the needs of regulations and standards. | |
Okta – Trial / Demo
8. Sophos
.webp)
Sophos is able to detect and respond to threats in real-time throughout its SaaS infrastructure by utilizing modern cloud-based security solutions. As a result, new dangers can be identified quickly.
Sophos applies strong encryption algorithms to safeguard data in transit, guaranteeing the privacy and integrity of data as it travels to and from the SaaS platform.
Stops illegal access and suspicious activity by checking user IDs and monitoring access patterns with Identity and Access Management (IAM) systems.
Using machine learning algorithms, Sophos is able to study user behavior, detect anomalous activity, and effectively prevent insider threats.
It has SIEM (Security Information and Event Management) features for centralized monitoring and analysis, which guarantees rapid incident response.
By configuring user rights according to their duties and responsibilities and protecting critical information, administrators can exercise precise control with granular access restrictions.
Features
- Keeps devices safe from malware, ransomware, and other advanced threats.
- Companies that offer network security use attack prevention and application control.
- Finds and stops online traffic that is harmful.
- Only lets approved devices connect to the network.
- Keeps mobile gadgets safe and under control.
| What is Good? | What Could Be Better? |
|---|---|
| Provides endpoint, network, and cloud cybersecurity solutions. | Incomplete SaaS app coverage |
| Facilitates management using simple interfaces. | Complex policies to configure. |
| Centralizes security for easier administration. | |
| Effectively blocks malware, ransomware, and sophisticated threats. | |
Sophos – Trial / Demo
9. Netskope
.webp)
Regularly comparing your SaaS app settings to various industry standards such as CIS, PCI-DSS, NIST, HIPAA, CSA, GDPR, AIPCA, ISO, and more is how Netskope protects your security.
Additionally, it gives risk ratings to your management, alerts any links to third-party apps, and monitors the configuration settings of your managed apps.
The inventory view gives helpful context by offering a clear overview of all resources and instances of SaaS apps.
The suggested syntax auto-complete capabilities of the Netskope Governance Language (NGL) make data inquiries for SaaS apps more approachable.
In addition, the powerful Netskope Security Cloud platform is the backbone of Netskope Intelligent SSE, providing real-time threat prevention, unmatched visibility, and accessibility for all cloud services, websites, and private apps, regardless of device or location.
Your security posture will stay strong and flexible in the face of ever-changing threats with this all-encompassing approach.
Features
- Keeps an eye on and manages cloud apps and files.
- Screens internet traffic URLs, protects against threats, and stops data loss.
- Keeps an eye on and stops data leaks in the cloud and web traffic.
- Cloud security rules need to be evaluated and followed.
- Protects entry to the network without trust.
| What is Good | What Could Be Better? |
|---|---|
| Secures cloud and web applications, essential in today’s digital world. | Planning and skills may be needed for deployment. |
| Granular cloud and web traffic visibility and control | Users may need time to master the platform. |
| Strong cloud DLP to secure sensitive data. | |
| Helps secure resource access with zero trust. | |
Netskope – Trial / Demo
10. Check Point
.webp)
As a dynamic stronghold armed to the teeth, Checkpoint fends off invaders. Strong firewalls essentially act as sentinels, carefully examining data packets.
This level of inspection creates an impenetrable barrier by ensuring that only authorized traffic can pass through. Internally, malware sandboxing and intrusion prevention systems (IPS) quietly detect and eliminate threats.
They make sure there’s no chance of infiltration. Now think about cloud-based SaaS products; these pose new security risks. These include the possibility of client data leakage, vulnerability to new forms of malware, and phishing assaults.
Checkpoint is leading the way in SaaS network security with its combination of technical expertise and user-friendly interfaces, resulting in a robust digital defense.
Features
- An advanced firewall that stops intrusions, controls applications, and provides a VPN.
- Malware, zero-day attacks, and other advanced risks can be stopped by real-time updates.
- Centrally manage and keep an eye on security rules and settings.
- To avoid getting malware, look at and separate things that you’re not sure about in a sandbox.
- Endpoints are kept safe by antivirus, anti-ransomware, and danger prevention.
| What is Good? | What Could Be Better? |
|---|---|
| Centralized management simplifies administration. | High maintenance costs. |
| Allows rigorous access controls with zero trust network access. | Complex rule management |
| Protects cloud and mobile settings. | |
| “Never trust, always verify” is their strict security policy. | |
Check Point – Trial / Demo
Conclusion
Many companies now rely heavily on SaaS apps due to the widespread adoption of digital transformation. However, the evolution to cloud-based solutions introduces new security concerns.
The accessibility of reliable network security solutions for SaaS is an essential requirement. Comprehensive security procedures protect not just the data but also the confidence of stakeholders and customers.
SaaS security solutions are becoming more necessary for enterprises to fully utilize the cloud while mitigating risks as cyber threats increase.
Modern, resilient, and successful businesses must combine SaaS with solid network security.
FAQ
If you’re going to use a cloud service, be sure it has strong encryption both while the data is in motion and when it’s sitting idle. Look into the platform’s security documentation or talk to the company behind it.
Yes, many SaaS apps can connect to third-party security tools like firewalls, intrusion detection systems, and SIEM systems.
SaaS applications need network security to secure sensitive data, maintain company continuity, build consumer trust, and meet regulations.


