Recently, on March 20, the well-known security company, Malwarebytes, recognized a targeted cyberattack upon household brand Tupperware and its associated websites that is quite active today. They tried to inform Tupperware shortly after their discovery, but none of their calls or emails were responded.
These threat actors negotiated the official Tupperware.com site, which equates close to 1 million monthly visits, and the attack affected the few of its localized versions simply by disguising ill-disposed code within an image file that initiates a false payment form during the checkout process.
Basically, this false payment form simply handles the customer payment data just like a digital credit card skimmer and then simply carries it on to the cybercriminals with Tupperware customers.
However, as per the Malwarebytes, the ill-disposed code on Tupperware’s website operates by copying the company’s official payment form. However, most of the time, a user initiates a payment, the ill-disposed code generates an iframe that hovers over the page and confers a cloned payment form, which simply looks like the Tupperware’s original VISA CyberSource payment form.
Thus, cloned form then gathers data accessed by users, such as first and last name, mobile number, billing address, credit card number, credit card expiry date, and credit card CVV code, and then simply transfers this information to a remote server.

However, “the criminals devised their skimmer charge so that customers first enter their data into the rogue iframe and are then instantly shown an error, covered as a session time-out,” said Jerome Segura, a malware researcher at Malwarebytes.
Rogue iframe container
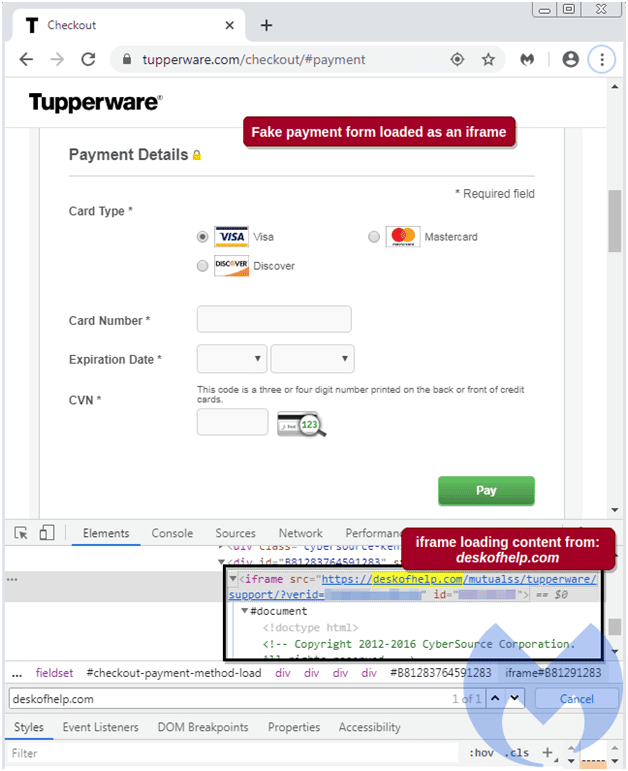
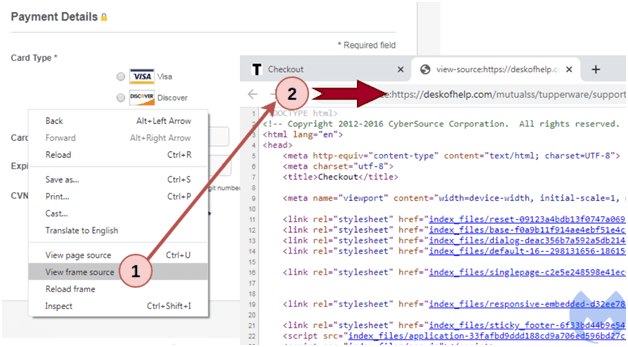
While at the time of their web crawls, they recognized a suspect-looking iframe placed from deskofhelp.com while attending the checkout page at tupperware.com. This iframe is capable of representing the payment form courses offered to online customers.
There are some red flags with this domain name, and here they are:-
- It was founded on March 9, and apart from this they have also noticed several fraudulent websites, recently-registered domains are frequently used by threat attackers simply to a new campaign.
- It is manifested to [email protected], an email address with Russian provider Yandex. This appears at odds for a payment form a US-branded website.
- It is treated on a server at 5.2.78.19 beside several phishing domains.
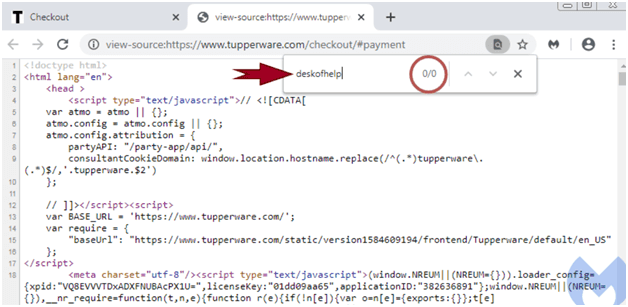
Moreover, if you want to investigate the checkout page’s HTML source code, then you would not recognize this ill-disposed iframe. As it is filled dynamically in the Document Object Model (DOM) only.
Not only this, but the criminals also devised their skimmer attack so that customers first enter their data within the rogue iframe and are then quickly shown an error, hidden as a session time-out. Thus, this enables the threat actors to reload the page with the authorized payment form. Therefore, Victims will start putting their information a second time, but, by that time, the data fraud gets accomplished.

Thus, to recognize how the card skimmer attack achieved, we required to go back a few steps and explore all the web resources that we have arranged, comprising image files. Upon recognizing this note, they simply requested Tupperware on the phone several times, and also sent messages through email, Twitter, and LinkedIn as well. However, at the time of communication, they didn’t hear any information back from the company, and the site persists to be compromised.
So, what do you think about this? Simply share all your views and thoughts in the comment section below. And if you liked this post then simply do not forget to share this post with your friends, family and on your social profiles as well.






