An 18-year-old Wisconsin teenager has been accused by federal authorities of a cyberattack that compromised 60,000 user accounts at the sports betting website DraftKings last year.
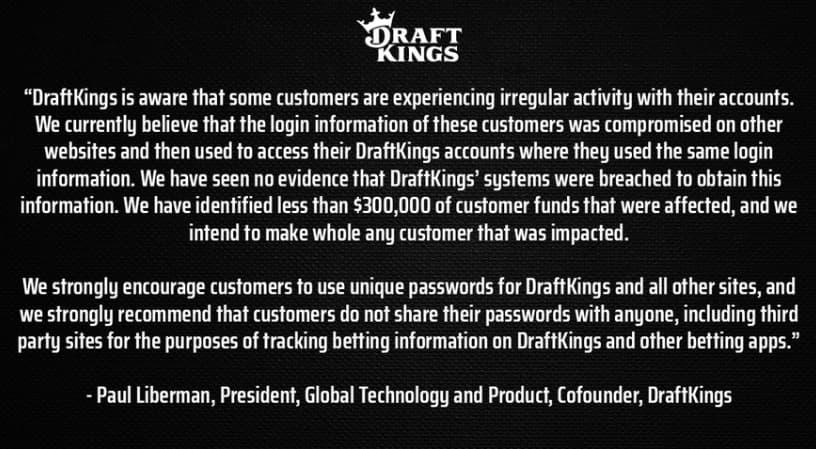
A “credential stuffing attack” was allegedly planned by Joseph Garrison to steal money from DraftKings user accounts.
U.S. Attorney Damian Williams said: “As alleged, Garrison used a credential stuffing attack to hack into the accounts of tens of thousands of victims and steal hundreds of thousands of dollars. Today, thanks to the work of my Office and the FBI, Garrison learned that you shouldn’t bet on getting away with fraud.”
During a credential stuffing attack, a cyber threat actor gathers stolen credentials, or username and password pairs, obtained from other significant data breaches of other firms, which are available for purchase on the dark web.
“The threat actor then systematically attempts to use those stolen credentials to obtain unauthorized access to accounts held by the same user with other companies and providers to compromise accounts where the user has maintained the same password.”, DOJ reported.
In this case, there were numerous attempts to log into the accounts of the betting website using a vast list of stolen credentials in connection with the attack on the betting website.
Through the credential stuffing attack, GARRISON and others could obtain access to almost 60,000 accounts on the betting website (the “Victim Accounts”).
The individuals who gained unauthorized access to the victim accounts were able to add a new payment method to the account, deposit $5 into it to verify it, and then withdraw all of the account’s funds using the new payment method (i.e., to a newly added financial account belonging to the hacker), stealing the victim account’s funds.
GARRISON and others used this technique to steal over $600,000 from 1,600 victim accounts.
Police Carried Out An Investigation
Law enforcement discovered almost 700 similar “config” files for dozens of corporate websites on GARRISON’s computer. These programs need unique “config” files for a target website to perform credential-stuffing attacks.
On GARRISON’s computer, law enforcement discovered files containing approximately 40 million username and password pairs, which are also employed in credential stuffing attacks.
Additional information implicating the defendant in the November 2022 credential attempt on the betting platform was discovered while reviewing Garrison’s phone, including conversations with co-conspirators about hacking the website.
During one of these conversations, Garrison also stated that he didn’t think law authorities would be able to catch him or bring charges against him because “fraud is fun. I’m addicted to seeing money in my account. I’m like obsessed with bypassing shit.”
Garrison also formerly managed a website called “Goat Shop,” where he sold user accounts that had been compromised. At its height, this site brought him $15,000 every day.
The FBI’s criminal complaints noted that Wisconsin police interviewed Garrison in June 2022, when he would have been a minor, suggesting that he was compelled to close the business.
He may spend decades behind bars if convicted of the accusations, which include conspiring to hack computers and committing wire fraud.
Common Security Challenges Facing CISOs? – Download Free CISO’s Guide





.webp)