Hiring and firing can be one of the most time-consuming and expensive endeavors many companies undertake. If you get it wrong, it won’t be long before there are issues within your team that are flagged up.
It gets more complicated when you need to hire for technical roles that might be out of your knowledge base. Some of the most challenging positions to hire for are those who deal with coding, security, and other technical roles.
But one thing is for sure; cyber security is vital for every company that does anything online.
As a business owner, you are aware that you need to ensure you have the most qualified cyber security on your team. As an example perimeter 81 offers a SASE security solution and you can combine with a team to create a security framework that works.

Why does your business need cyber security?
There has been a significant rise in businesses that offer a hybrid way of working or hiring entirely remotely in the last few years. This means that more people are accessing your business network – and some of them might not have the appropriate training to ensure what they do is safe.
Having a cyber security team will mean that your sensitive information, systems, and all of your valuable data are kept secure.
When a company doesn’t have a robust cyber security strategy, it will be unable to defend itself if they were the victim of a cyber attack.
The world is more connected than ever, and with all of these advancements, the risk of a cyber-attack has increased. As quickly as a business adopts new technology, cybercriminals will find a way to penetrate the systems.
Having a team, including highly skilled managers, is the one line of defense that will stop would-be cybercriminals in their tracks.

What are the benefits of hiring a CISO manager and IT manager?
One of the most complex and challenging aspects of any business is the speed at which security evolves. No matter how big or small your company, you are at threat of security breaches, and it is, unfortunately, a fact that these breaches are becoming more common.
A Chief Information Security Officer is no longer a member of staff that is nice to have; it is a must. It can be in the form of a remote role, in-house, ad-hoc, or via a specialist company. What matters is that you have someone who has the security of your business in mind all the time.
They will be the first to call for training and education on risks and risk management. Not only that, but a CISO will have the final say on all things cyber security and make information-based suggestions.
An IT manager will be able to work with your IT team to ensure that the strategy in place is the best for the company. Ensuring that they have a framework that enables scaling, growth, productivity, and support. Your IT manager will understand your company’s business goals and be able to proactively prepare you and your team for the future.
The benefits of hiring both of these roles are:
- Speed of recovery when incidents happen
- Prevention of cyber attacks
- Well trained staff, and education
- Compliance
- Improve profitability
- Increased productivity
- Reduction of costs
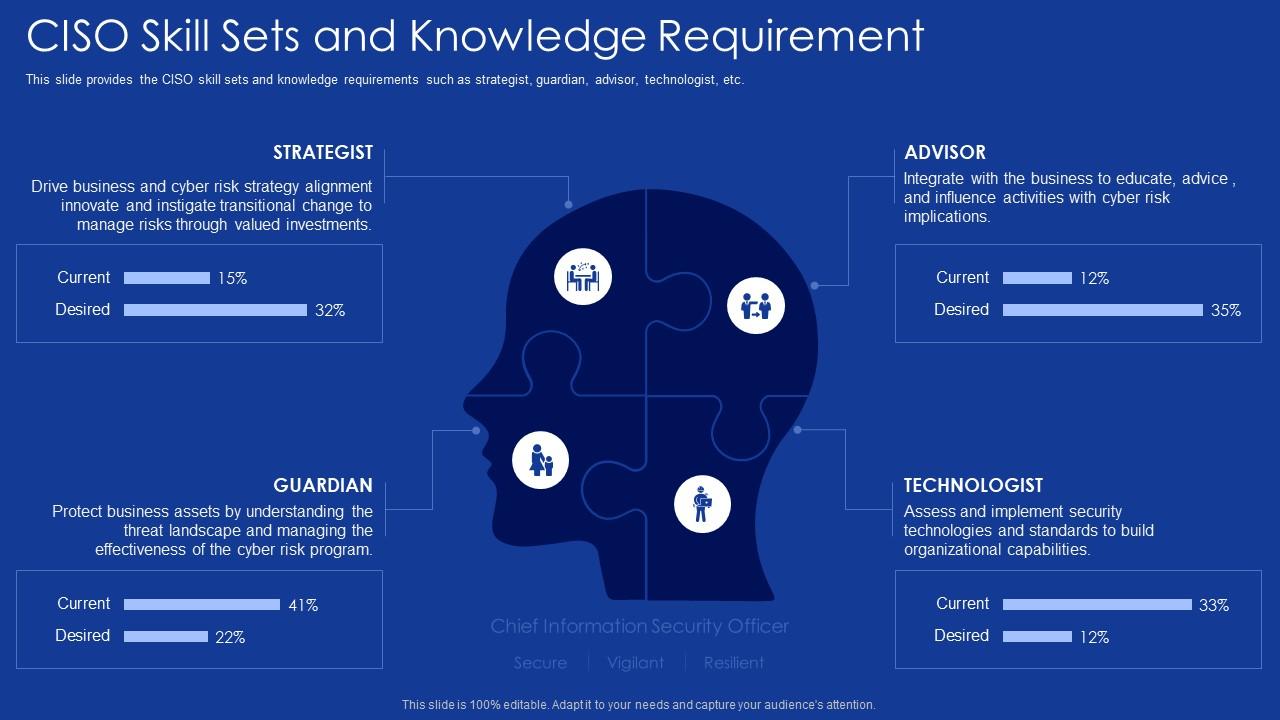
What skills should you look for when hiring a CISO and IT Manager?
While some of the skills will vary by the role, there are some skills and characteristics that you will be looking for in both.
Risk assessment and management
To be great at what they do, both IT and CISO managers will need to have a high-risk assessment and management experience. While reviewing the CV and during interviews, ask for examples of when this was done. Most stakeholders, board, and C-suite will be looking for risk management.
Regulations and Compliance
When hiring for these roles, the person should be an expert in regulations and compliance. This is what keeps your business protected and up to standard. All of your policies should be relevant and effective.
Supervisory Skills
You might choose to have a team or work with a company with a team. Either way, your IT manager or CISO will need proper leadership skills. At all times, they will need to make sure that the team is on track, working well together, and staying on top of training.
A team that is engaged and supported will consistently outperform groups that lack proper supervisory skills in the leadership.
Incident management
If the person you hire hasn’t dealt with any incidents, you can’t be sure that they will work well under pressure. They will need to take a systematic approach to what they do.
When posed the question about how they might handle an incident, you are looking for these steps:
- Preparation
- Identification
- Remediation
- Post-incident activity
How they do it might vary, but these are the very basics.
Policy Development and Administration
Your CISO and IT managers will be the people developing security policies that meet the needs of the business. They should be easy to implement throughout the company, secure your environment and meet all regulations and legal requirements.
Software
Many teams will create their solutions; in-house solutions are common when the CISO or IT management can’t find a robust solution to work for them. At a minimum, they will be able to work with Network security software, data privacy, operations technology, and security automation software.
What percentage of those that they use will vary based on your business.
A surprisingly small number of businesses have a full-time IT manager or CISO, and as such, they remain at risk of a cyber-attack. The financial cost of a data breach and the reputation can force many smaller companies to close.
Don’t put your business at risk.
Remember that it’s not just small companies that can suffer from a data breach: Data Breaches Archives – Cyber Security News.





%20(1).webp)