As per the new report from FireEye, most cyberattacks happen outside of working hours – either on weekends or in the evening. Well, Ransomware is basically a type of digital blackmail, it is disruptive and costly, and it influences all varieties of organizations, from the wool industry to the making edge space technology firms.
Initial Infection Vectors
After analyzing “dozens of ransomware conflict response investigations” from 2017 to 2019, the firm obtained that there are three-quarters.
Thus, all ransomware attacks in the business sector simply occurs outside of regular working hours. However, infections have urged hospitals to turn away patients and law enforcement to withdraw cases against drug traffickers.
Ransomware operators have lately begun mixing encryption with the threat of information leak and display to improve leverage against victims.
There may be a silver covering; however, Mandiant intelligence research recommends that concentrating on preventive efforts in crucial areas and responding quickly may enable organizations to stop Ransomware before it is disposed of.
As per the report, one of the most regularly witnessed vectors was an attacker logging on to a system in a victim environment through the Remote Desktop Protocol (RDP).
Well, a significant number of ransomware cases were connected to phishing campaigns producing some of the most productive malware families in financially motivated actions.
Various ransomware infections were drawn back to a user in the victim environment traveling to a settled website that appeared in a DRIDEX infection.
Ransomware Deployed Most Often After Hours
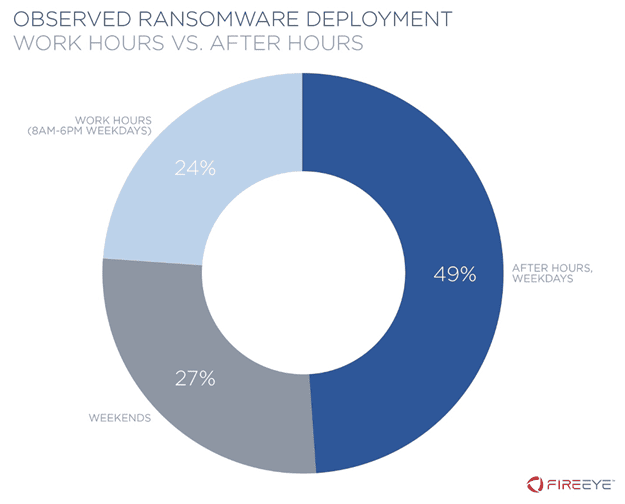
Nearly, in 76% of conflicts they studied, Ransomware was effected in victim situations after hours, which is most likely in the weekend or before 8:00 A.M. or after 6:00 P.M. on a working day, utilizing the time zone and ordinary workweek of the victim system.

This investigation emphasizes that threat actors remain working even when most employees may not work.
The attackers want to maximize the inherent effectiveness of the operation so that any remediation effort will be completed more slowly than they would be through regular work hours.
Mitigation Recommended
Well, organizations attempting to stop or mitigate the consequences of Ransomware could count the following steps, and here are they:-
- Check and remediate infections immediately to stop attackers from transferring follow-on activity or selling access to other threat actors for additional exploitation.
- Implement multi-factor authentication, that is, where permitted, do not allow single-factor authentication for users who have not set up the multi-factor device.
- Complete network segmentation simply to stop a possible infection from growing.
- Generate regular backups of essential data needed to secure business continuity and, if attainable, collect them offsite, as attackers frequently target backups.
- Secure after-hours coverage is ready to answer inside a set time period in the matter of an emergency.
So, what do you think about this? Simply share all your views and thoughts in the comment section below. And if you liked this post, then simply do not forget to share this post with your friends, family, and on your social profiles.