Resecurity, Inc. (USA) noticed a spike in phishing content delivered via Azure Front Door (AFD). Azure Front Door is a modern cloud content delivery network (CDN) service that delivers high performance, scalability, and secure user experiences for your content and applications.
The analysis says the malicious campaigns imitate various services appearing to be legitimately created on the “azurefd.net” domain. Therefore, this permits the bad actors to trap users and spread phishing content to intercept credentials from business applications and e-mail accounts.
The phishing resources target SendGrid, Docusign, and Amazon customers, major Japanese and Middle East online service providers, and corporations.
The researchers say, “The threat actors are leveraging compromised business and personal e-mail accounts to deliver spam containing phishing links to fake WEB-resources hosted on Azure Front Door, as such domains are typically whitelisted or treated as legitimate by the end-user.”
Cybercriminals Leverage Compromised e-mail Accounts
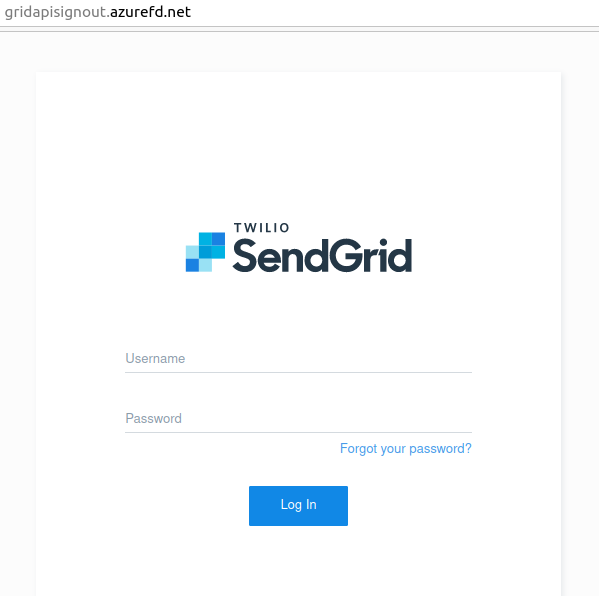
Researchers observed a fake billing notification sent on behalf of SendGrid, a Colorado-based customer communication platform for transactional and marketing email.
Based on the analysis, the attackers are utilizing an automated way to create their phishing letters, so that they can scale their campaigns to target a broader number of customers globally.
“The observed de-obfuscated source codes of the phishing scenarios contained the signatures “STRAT Check” and references to WHOIS-protected domains registered in “.click” and “.xyz” domain zones to collect compromised credentials”, say the Cybersecurity researchers from Resecurity.
In addition, the new wave of phishing attacks used multiple domains and a few of which are hard to differentiate from legitimate correspondence due to their naming and reference to Azure Front Door.
To reduce the risk from this activity, the malicious domain names and additional intelligence have been reported by Resecurity to Microsoft Security Response Center (MSRC).
Therefore, the overall Business E-mail Compromise (BEC) or Email Account Compromise (EAC) statistics reported to the FBI IC3, law enforcement and derived from filings with financial institutions between June 2016 and December 2021 exceeds 43$ billion.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates.