As per Raccoon Stealer, it has been found that the malware is being distributed by the website network which acts as a “dropper as a service”. They are serving different types of malware packages where it is often bundling the unwanted malware in a single dropper. These include all kinds of assortments like click fraud bots, ransomware, information stealer, and much more.
This campaign took place between January and April 2021. Additionally, They are distributing other malicious content in the same site. Few websites use the ‘cracked’ version of the enterprise software and the link they share with the network domain which is directly redirected with the victim.
Researcher of the Raccoon Stealer Campaign has discovered multiple cases where they are they have tried things with other malware campaigns. For example, they found the information stealer, Conti, clickfraud bot, etc.
Click Bait Pages To Download Software:
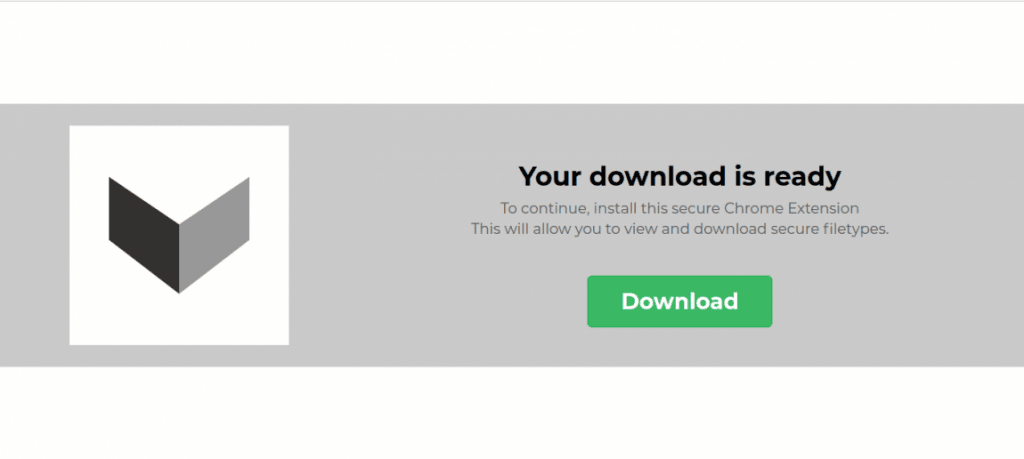
On most of the bait pages, they have hosted a WordPress blog platform. They download the button and link that with another host. There is a passing set of parameters, which include package name with affiliated identifier code for the application. It redirected the browser session to the intermediary site before it arrives at its destination.
As soon as visitors arrive, sites will give prompt notification, and they will allow websites to send false malware alerts. When the user clicks on that alert, that will direct to the website till the visitor’s destination come.
That time much-unwanted application and malware gets downloaded, to stop that ransomware user need to install Glupteba backdoor.
Due to the dynamic delivery network, things act as an intermediary between the download site and bait sites. Therefore, there are few fake cracked products that can do multiple malicious campaigns at the same time.
Delivery Mechanism
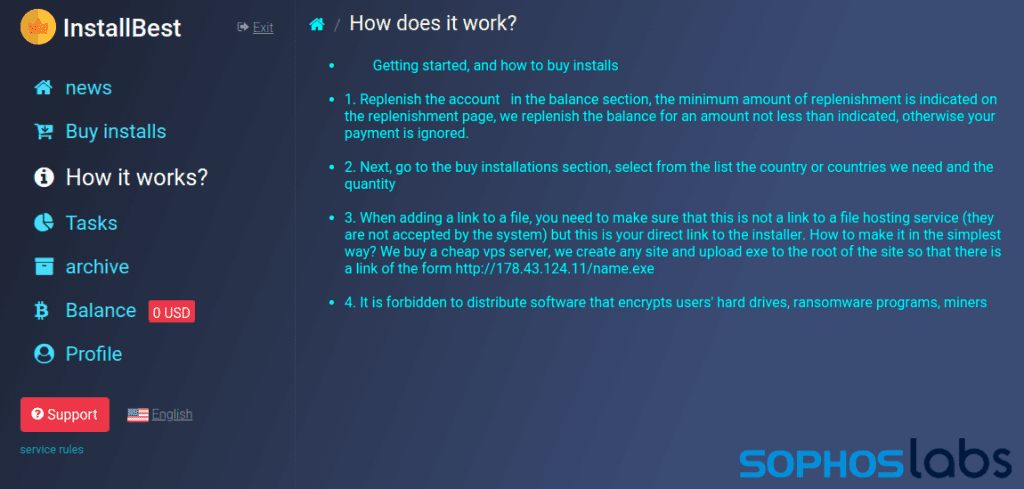
“Traffic exchanges” are always on standby for the malware campaign. The marketplace has “software installs” which is a part of the toolkit mainly used by entry-level criminals who want to spread malware.

The above image indicates the best practices that recommend Cloudflare, which is based on the downloaders. However, as per the discovery by someone, it is true that few installers are on discord.
Malware Acts as a Middlemen:
In this, they have few services which have made their way to deliver the network. Another way is to go between the established traffic suppliers, which includes the malvertising network, which is a blog publisher for the traffic.
Image
Above there is an InstallUSD site that allows owners to register and publish the downloaded link, but users need to require complete registration through Skype chat. It is mainly uncovered by the Facebook page, and this purport to crack the software downloads.
While Raccoon Stealer investigation they have found the campaign that deploys the information which is stealing the malware via .zip archives. All these types of files get traced with several websites with a cracked version of the software package.
The downloads, please: The file got to download, and as per the delivery method package got dropped with some essential characteristics. This download file has the .zip archive file, which is named cracked, and it also has a password







