Researchers identified the APT hacker group is the actual operator behind the Evilnum malware. This hacker group has been active since 2018 and mainly focuses on the companies in the financial sectors that provide trading and investment platforms and tools.
Evilnum APT hacker group has developed a set of malicious tools that combine Evilnum malware, legitimate utilities, and tools purchased from a Malware-as-a-Service (MaaS) provider; all these are used in attacks that the group makes on financial technology companies.
Attackers Used C# Component
Here, the threat actors start the attack with spearphishing emails containing files with .link extension, pretending to be an image or a document, and saved on Google Drive. Once the victim opens it on arrival, a malicious JavaScript component starts automatically.
The attackers use the function of the JavaScript component to implement other malware like the Evilnum spy module, Golden Chickens, MaaS, and multiple Python-based tools. Another malicious component developed in C# was also discovered, which also offers functions like the JavaScript component.
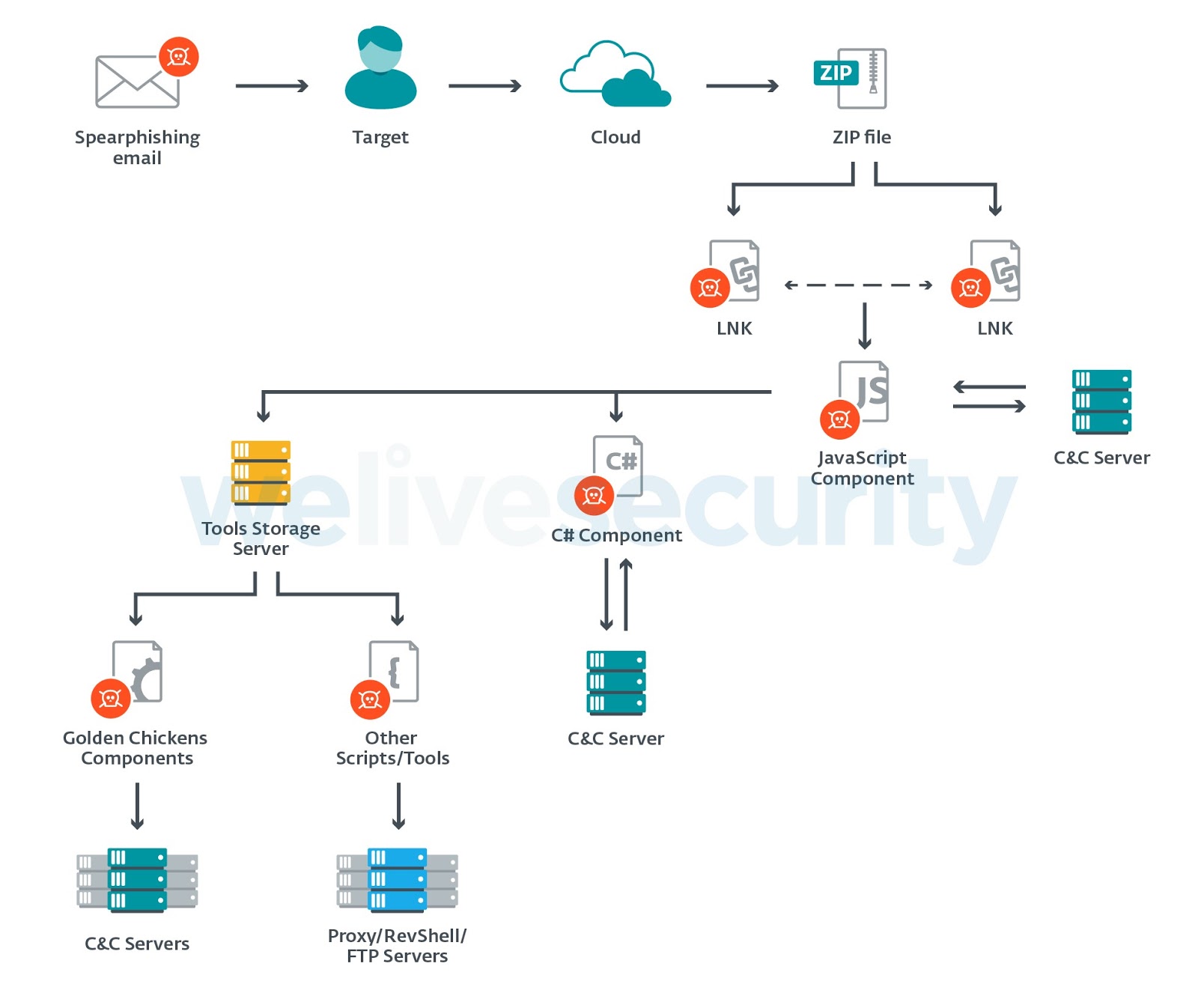
According to the ESETsecurity reports, the operations carried out by this hacker group involves several components, which were run independently and connect to different command and control (C2) servers to receive commands and tools. In the above image, you can see the whole operation map and the type of files that were used.
Data Involved
Since the threat actors target the fintech companies, here the hackers steal sensitive company and customer data like:-
- Spreadsheets and documents with customer lists.
- Investments and trading operations.
- Internal presentations.
- Software licenses and credentials for trading software/platforms.
- Cookies and session information from browsers.
- Email credentials.
- Customers’ credit card information.
- Customers’ proof of address/identity documents.
In these events, the attackers used spear-phishing emails to contact the employees of the attacked companies those who work in support and customer service segment. These employees are the ones, who are eligible to handle and receive identity proofs and credit card information from customers.
Payloads Used
The security researchers detected that the operators of Evilnum malware used Golden Chickens’ tools broadly; here the payloads used are mentioned below:-
- More_eggs
- A Meterpreter payload that we will call TerraPreter
- TerraStealer
- TerraTV
Moreover, the hackers also used Python-based tools and here they are:-
- Reverse shell over SSL script
- SSL proxy that uses PythonProxy, junction, plink, and stunnel.
- LaZagne
- IronPython
All these tools are used by the attackers to circumvent the security controls and NirSoft utilities to elicit and convey passwords, take screenshots, self-delete the malware, fetch and send cookies, software licenses, and VPN configurations.
Also Read:
Alina – A Point of Sale (POS) Malware Abusing Global DNS Traffic To Exfiltrated The Credit Card Data
FAKESPY – An Android Malware steal SMS messages, Application, and Financial data Around the World
Beware of New Mac Malware Spreading via Poisoned Google Search Results